Avast releases a new ransomware decryption tool for XData ransomware.
XData ransomware was discovered mid-May and now, two weeks later, we have released a free decryption tool for victims hit by XData ransomware that they can use to decrypt their data.
XData shares some similarities with the WannaCry ransomware that spread around the world. XData started spreading shortly after the WannaCry outbreak and has also been infecting machines by taking advantage the EternalBlue exploit.
The spreading of XData was definitely not as massive as WannaCry, but it still made an impact. As originally reported by the MalwareHunterTeam, it mainly targeted users in the Ukraine.
Here are stats of blocked XData attacks on our userbase:
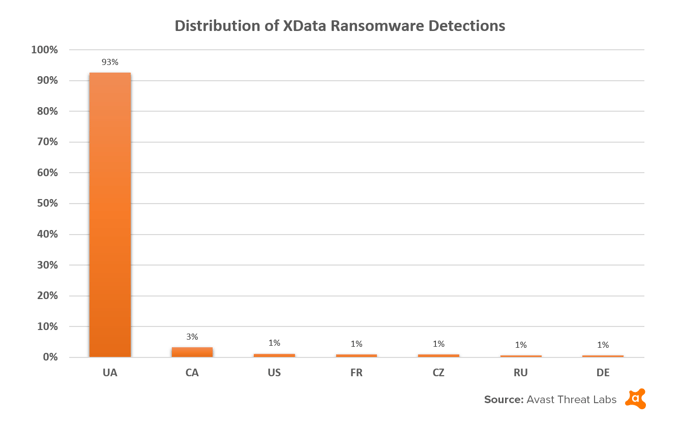
Stats from 2017-05-18 to 2017-05-31
Taking a closer look at XData’s code, we found that it is almost identical to another recent ransomware strain called AES_NI, for which we also have a free decryption tool. This code similarity is not an accident. AES_NI’s code has been allegedly stolen from its authors by the operators of XData.
XData Decryption
After infecting a machine, XData adds the ".~xdata~" extension to the encrypted files and drops the payment instructions in files named "HOW_CAN_I_DECRYPT_MY_FILES.txt".
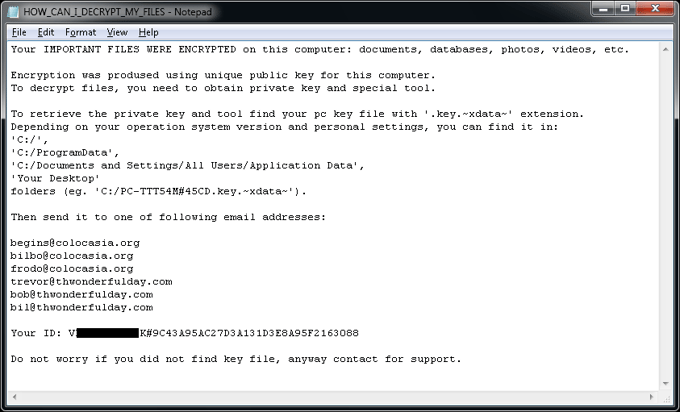
Additionally, the ransomware creates a key file with a name similar to:
[PC_NAME]#9C43A95AC27D3A131D3E8A95F2163088-#-20175267812-78.key.xdata in the following folders:
- C:\
- C:\ProgramData
- Desktop
To further copy AES_NI’s authors, who released the decryption key last week, the criminals behind XData also released their decryption key yesterday.
This allowed us to prepare a free decryption tool, which is located on our usual site.
Tips on how to avoid ransomware
- Install antivirus on all devices possible, including on your smartphone. Antivirus will block ransomware, should you encounter it.
- Updating all of your software whenever a new version becomes available can help prevent ransomware from exploiting a software vulnerability to infect your device.
- Being cautious can also greatly help avoid ransomware. You should stay away from shady websites, be careful what you download, and not open any links or attachments sent to you from a suspicious or unknown sender. Many people don’t think an ordinary Word or Excel document can lead to something malicious downloaded, which is why cybercriminals like using them for their attacks. Malicious attachments, sent in the form of a Word or Excel document, often request macros to be enabled, which allows the document to download malware, including ransomware, from the internet.
- While it cannot help you avoid ransomware, backing up your data on a regular basis will help avoid data loss, in case you fall victim to ransomware. If you regularly backup your data, while offline, to an external hard drive that is not connected to the internet, you greatly lower the risk of anyone touching your data through the internet.
Special thanks
A special thanks goes to my colleague Ladislav Zezula for preparing this decryptor.
IOCs
92ad1b7965d65bfef751cf6e4e8ad4837699165626e25131409d4134f031a497
d174f0c6ded55eb315320750aaa3152fc241acbfaef662bf691ffd0080327ab9