This year's report records a rise in ransomware as well as a jump in social engineering-based breaches
What a year it has been. Nothing delineates things more than reviewing the annual Verizon Data Breach Investigations Report (DBIR), which was published earlier this month. We wrote about last year's DBIR at this time of year. To refresh your memory, it's based on Verizon's assessment of breach data coming from a variety of sources called VERIS.
This year, there are links to its open source collection (if you want to do your own analysis), or a link to file your own (and anonymous) report in the interests of total transparency. Verizon’s team analyzed more than 29,000 incidents and 5,000 actual breaches.
The report states, “breaches are moving toward social and webapp vectors, and those are becoming more server based, such as gathering credentials and using them against cloud-based email systems.”
To no surprise, phishing increased from 25% of breaches in 2019 to 36% in 2020, aided by the various Covid-themed lures. Also, ransomware loomed large and doubled its frequency from 2019 to 2020 to 10% of the breaches, as you can see in the below chart.
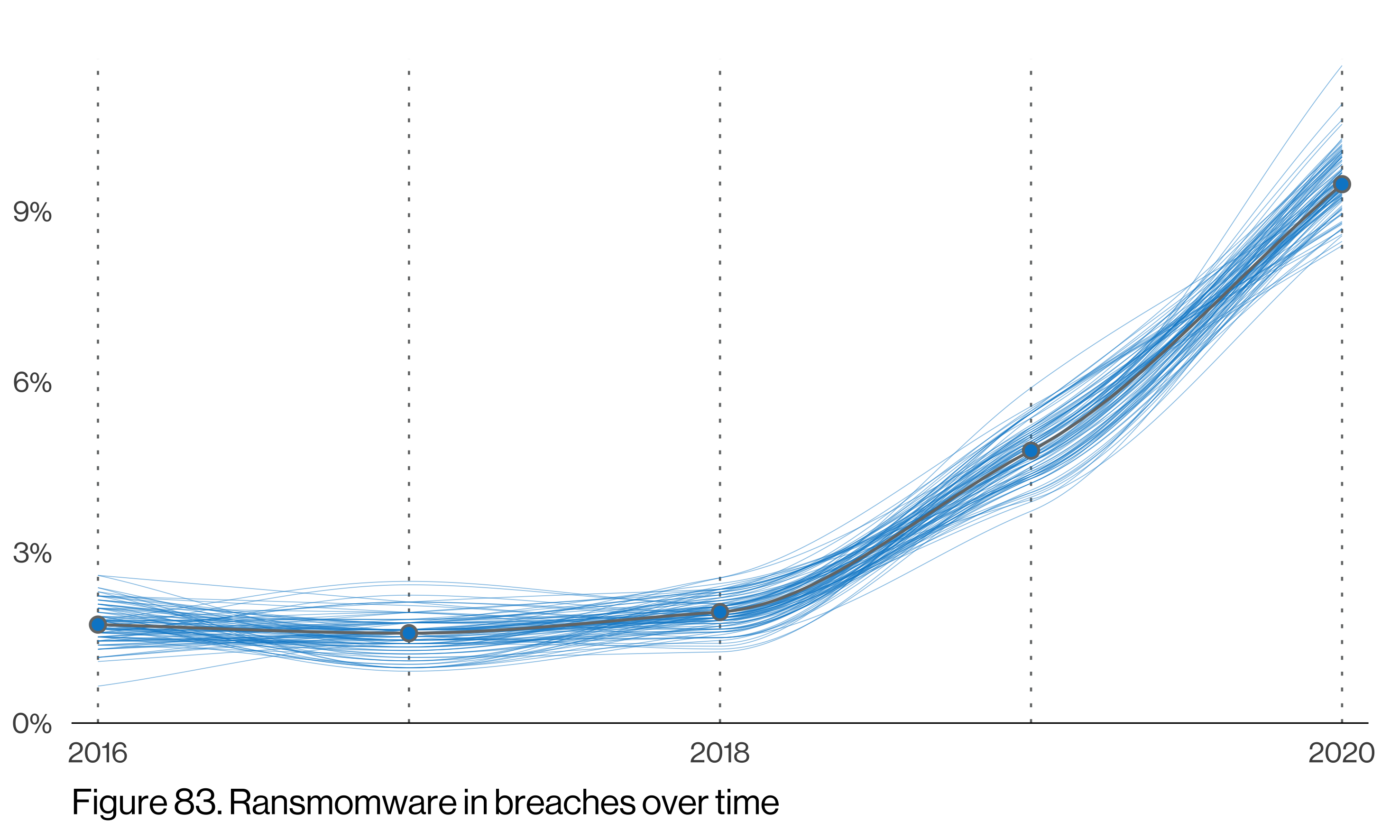
Image credit: Gabriel Bassett (GitHub)
The report cites a troubling trend where "actors have adopted the new tactic of stealing the data and publishing it instead of just encrypting it." In half the incidents reported, the vast majority of funds that were paid for ransoms — 99% — were held in accounts that were subsequently frozen and eventually recovered. The report suggests that “If your organization experiences an incident, we highly recommend that you contact the local branch of your national law enforcement and seek their assistance. Or, better yet, get to know them before the breach occurs!”
In addition to the rise in ransomware, another trend is a jump in social engineering-based breaches, which continues this growth that was first reported back in 2017. The report says this is connected to the rise in cloud-based email compromises. One big part of social engineering is the success or failure of various phishing lures. The DBIR analyzed 150 different phishing templates in this year’s report and examined the click-through rate, as shown in the chart below. While there is a wide range of success rates, the overall average has decreased to three percent.
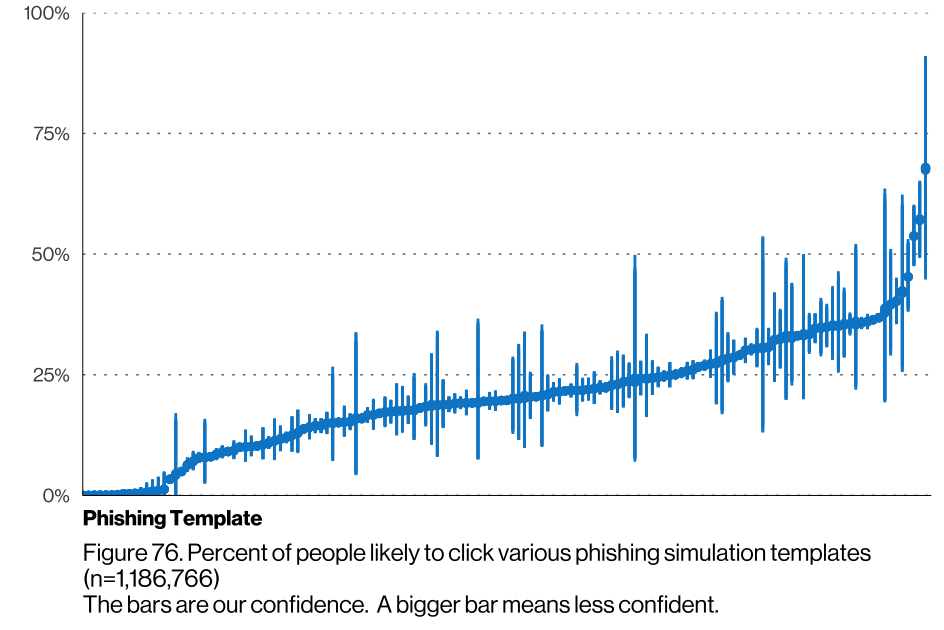
Image credit: Gabriel Bassett (GitHub)
A big part of social engineering-based attacks were business email compromises, whereby attacks pretend they are a manager at your company and try to get you to do their bidding. In the past year, there has been a jump to almost 10% of all non-denial-of-service (DoS) incidents. Back in 2016, these attacks were less than one percent of these incidents, and more than half of these compromises resulted in actual payouts to the attackers.
Speaking of DoS, you can see its continual rise over time, with it once again being the leading incident cause. DoS incidents have a median attack rate of 1.3Gbps, which is close to what was observed last year.
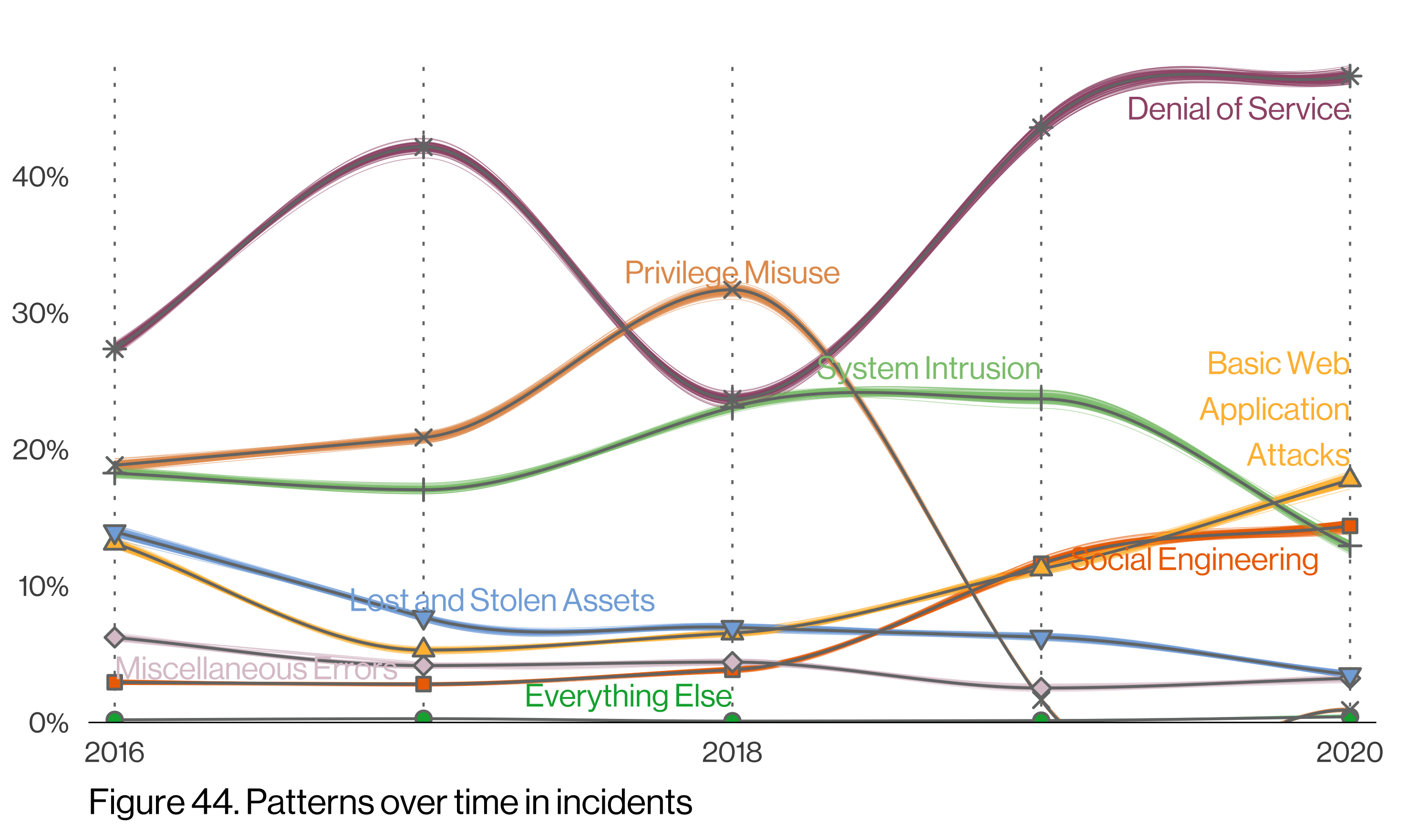
Image credit: Gabriel Bassett (GitHub)
One interesting change from last year’s report is that overall breach trends have followed similar patterns, no matter the size of the business affected. A total of a thousand incidents and 260 breaches were confirmed from smaller businesses or those with less than 1,000 employees. The differences between the smaller and larger organizations have largely disappeared from the DBIR in 2020.
“Last year we reported that smaller organizations seemed to be doing better in terms of discovering breaches more quickly than their larger counterparts. This year’s data shows that large organizations have made a shift to finding breaches within 'Days or less' in over half of the cases (55%), while small organizations fared less positively at 47%.” The report also found that “you don’t have to be a large organization to have a good chance that one of your members has received a malicious URL or even installed a malicious Android app.” Once your company has more than 100 or so employees, the chances are almost 100% that both of these events will happen to someone in your company.
Further reading:
How do hackers get into a company's network?
Cybersecurity best practices for small to mid-sized businesses