Learn more about the top breach trends of the year and what to look out for to keep your business safe
Today Verizon published the latest 2020 Data Breach Investigations Report (DBIR). What sets the DBIR apart is that it combines breach data from multiple sources using the common industry collection, VERIS, a third-party repository where threat data is uploaded and made anonymous. This gives the report a solid authoritative voice, which is one reason why it’s frequently quoted by the security community. Report citations also come from vendor telemetry sources, so it is also a bit self-referential. (Avast has not participated in this effort.)
Overall breach trends
One of the biggest trends is the declining popularity of malware which has been knocked out of the top three causes for a breach for the first time. Breaches involving web-based applications are on the rise, topping the list this year. In second and third place were compromised desktops and mail servers. This is because so much more business is being done through web-based apps that criminals are going after credentials to gain access to these assets.
Last year’s DBIR cited 60% of all web app compromises happen with the front ends to cloud-based email servers. Having careless cloud users is certainly something to watch out for. Speaking of carelessness, keeping track of your server assets is a second issue. Many of the breaches happened on large networks that span multiple internet providers and across regions. If you are going to deploy a solid patching program, make sure you can first locate all of your servers. “We are seeing more assets which are flying beneath the radar and not immediately being patched,” said Gabriel Bassett, one of the report analysts in a conversation with me last week.
Also on the wane were trojan-based malware, which saw a drop of 15% in the number of attacks when compared to last year’s data.
SMBs are very different from larger businesses
The divide between small and large business has been narrowing over the past few years. And this trend has continued, according to a special analysis in this year’s DBIR. SMBs are increasingly more cloud-savvy, and the criminals have adjusted their tactics accordingly. The authors compare the current situation with what they saw in 2013. Breaches are still more than twice as common with larger (more than 1,000 employees) than smaller businesses. Back in 2013, the top issue was spyware for SMBs, whereas nowadays it is all about web apps. In 2013, the favorite target was stolen payment card data, while today it is credentials that are more popular. “Nowadays, organizations regardless of size are troubled with attacks on user devices, mail servers and social attacks,” the authors stated. One bright spot for SMBs is that breaches take much longer to discover in larger organizations: months vs. days, possibly due to the latter’s reduced attack surface area. (see below graphic)
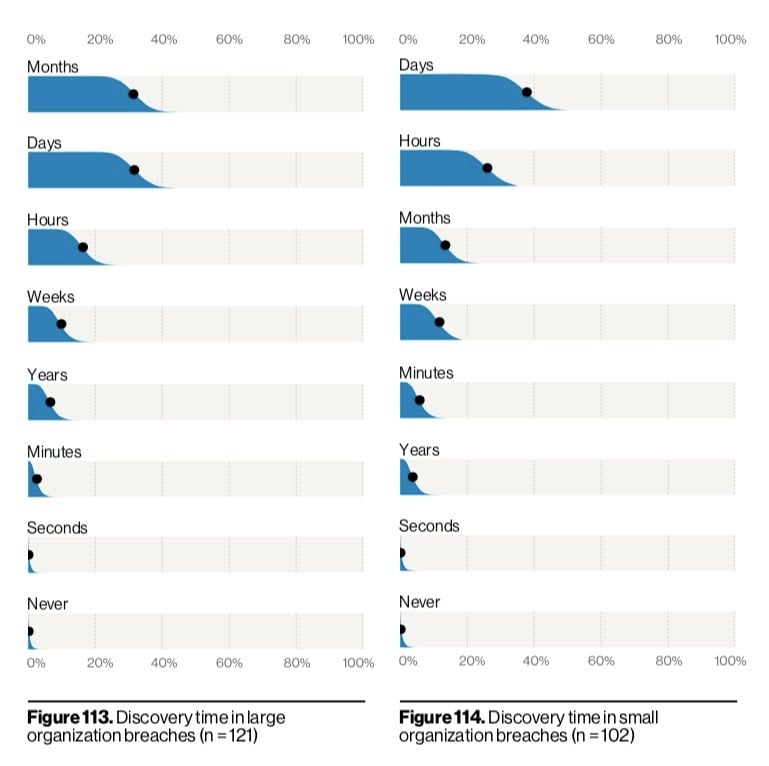
Source: Verizon's 2020 Data Breach Incident Report
Ransomware trends
As was mentioned in Avast’s blog post on WannaCry’s third anniversary, ransomware still plagues the internet. Back then, hackers broadly sprayed WannaCry across the globe and did significant damage. But today’s ransomware attacks are much more targeted and involve doxing – taking very selective targets as a means to pressure victims to pay up like a blackmail scheme. This is echoed in this year’s DBIR report, which concurs that ransomware is on a slight rise of a few percent. “We see ransomware popping up like a poor relation demanding money—which, in many cases, they get. It should be on your radar,” says the report’s authors. According to the report, ransomware was responsible for 27% of total incidents they tracked. It was also the third most common malware breach method. Ransomware also accounts for 80% of infections in the educational sector and is second in popularity across many Asian-based networks. And certainly ransomware is breaking records: there was a recent Sodinokobi-based ransomware attack on the law firm of Grubman, Shire in New York City. This is where more than 750 GB of personal data on famous entertainment clients such as Madonna and Lady Gaga were stolen.
To view the full report, visit https://enterprise.verizon.com/resources/reports/dbir/