These threats demonstrate how attackers can take advantage of just about anything with an internet connection.
Security researchers have uncovered a new series of threats that are targeting uninterrupted power supply (UPS) units. These threats can result in malware attacking the computers connected to the same networks through a variety of clever mechanisms. The US Cybersecurity and Infrastructure Security Agency (CISA) has discovered that the attacks have already been reported to the US Department of Energy.
The modern UPS is more than just a big battery that switches on to power up computers in emergencies — on the contrary, it has sophisticated circuitry along with network connections and software that works in conjunction with cloud-based management tools to report on its status. These functionalities also make it possible for IT managers to observe the status of a UPS unit and control its operation. As a result, many modern UPS units have internet access, which makes them vulnerable to cyberattacks.
Researchers found a new series of attacks called TLStorm-WP, which is documented with vulnerabilities CVE-2022-22805, CVE-2022-0715 and CVE-2022-22806. The name references weaknesses in the TLS (Transport Layer Security) protocol used for the UPS units’ internet connection. The attacks affect most of the Smart-UPS devices with the SmartConnect feature sold by APC, a major UPS manufacturer.
Attackers can leverage UPS units’ internet connection and trick the UPS into updating its firmware with something that includes malware to allow untrusted remote code execution. This serves as the entry point to an enterprise’s network. Another potential threat is that a compromised UPS unit could deliver power that could destroy connected computers.
The following diagram shows how the three attacks are related:
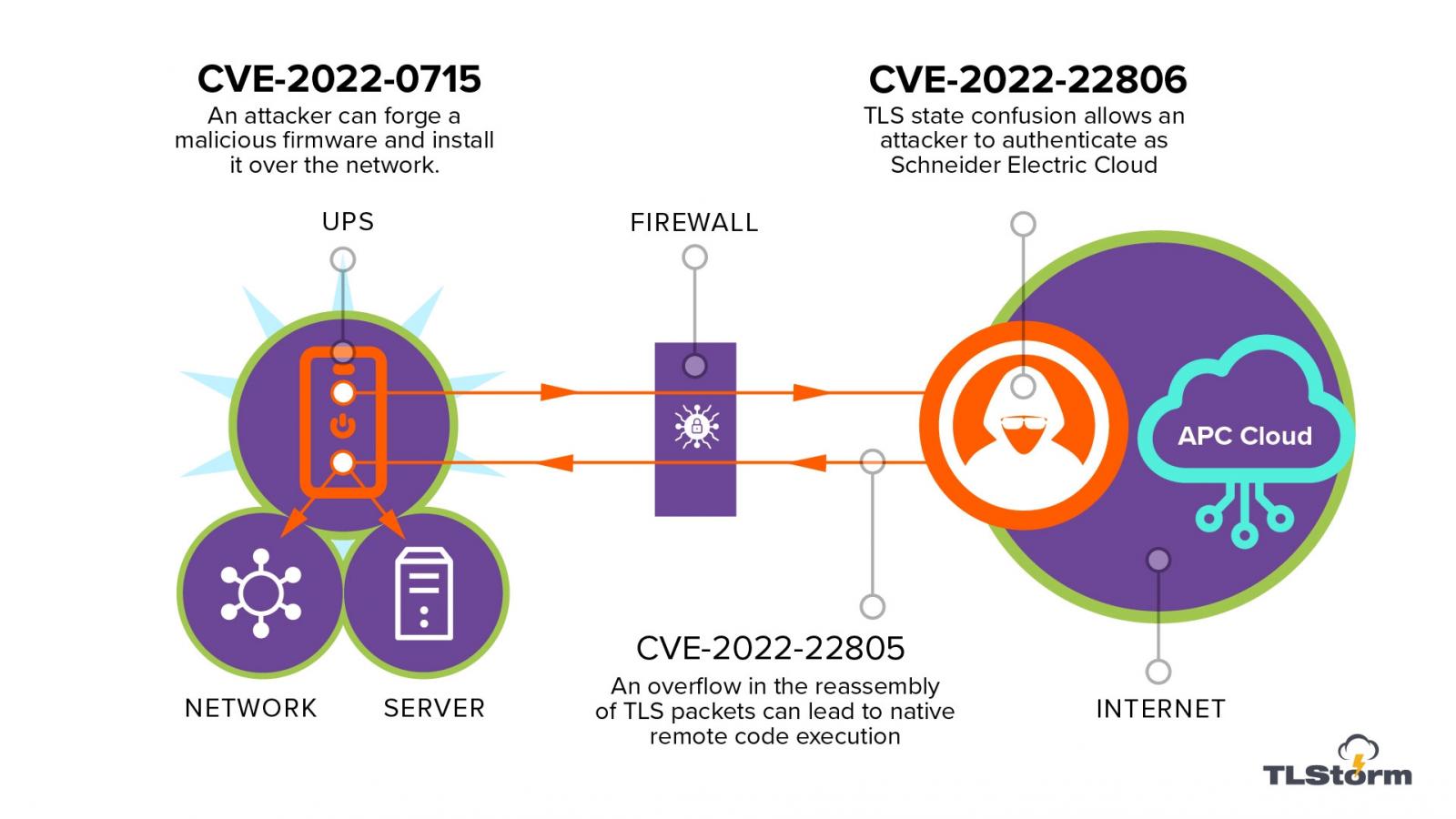 Image credit: Bleepstatic
Image credit: Bleepstatic
These issues highlight the risks that come along with large-scale IoT devices and how attackers can take advantage of just about anything with an internet connection. As is stated in Bleeping Computer, “Considering that vulnerable APC UPS units are used in about eight out of 10 companies and the sensitive environments they serve, such as medical facilities and server rooms, the implications can have significant physical consequences.”
What should you do if your UPS unit has been affected?
CISA recommends the following actions if you own a compromised UPS unit: