"Simple tools" allow regular people to participate in DDoS attacks in aid of Ukraine. But these tools are not safe, say Avast Threat Labs researchers.
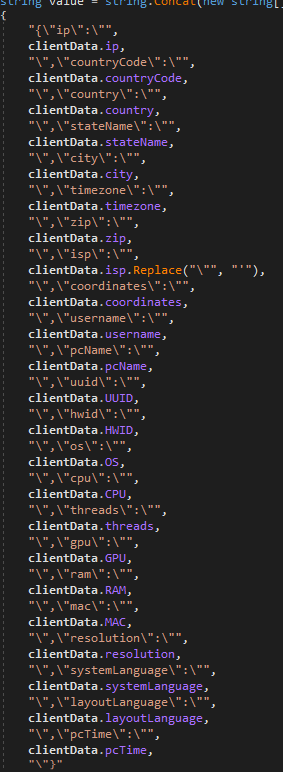
We have identified initiatives being shared through social media that encourage regular people to become hackers, by downloading DDoS tools to support DDoS attacks on Russian targets. The analysis of one of these tools shows that it isn’t secure, as it collects personal data that can make users identifiable, such as your IP address, country code, city, location derived from IP address, user name, hardware configuration and system language. Since the configuration is downloaded from a remote server, the tool can also support a DDoS attack on any target the server operator/ tool author picks without you knowing.
For example, take the disBalancer program that was even picked up by major media. We have seen about 900 of our users in Ukraine installing this program in order to conduct DDoS attacks on Russian websites. 
The first thing this program does is register the user, including personal information like location (derived from the IP address) and username. When the user starts the attack, this registration runs in the background without their knowledge.
This information runs over the unencrypted HTTP protocol to the C&C server, which means it can be easily intercepted. Additionally, there’s no way to know what site you’re attacking, so you have to trust the author about the sites they claim to target.
As a worst case scenario, the C&C server could become compromised, in which case all of the people joining this attack could be identified by location and username. That not only would put them in danger, but they could also be tricked into attacking a different target.
Although people might find it compelling to join these cyber forces as a way to voice their opinion on the war, it is still a cyber attack with all consequences. Users may think these tools provide a way to anonymously attack certain targets, however they don’t protect the privacy and anonymity of the user, and can put the person at risk of retaliation attacks.
We strongly recommend that people do not engage with these initiatives, as they will escalate the situation and the “simple user friendly tools” shared through these initiatives can be a privacy and security risk for the person downloading it.