Cybercriminals are using Facebook’s app platform to display a phishing page under the legitimate Facebook domain and TLS certificate.
A new phishing campaign takes advantage of Facebook’s security measures in order to appear legitimate.
In this case, the creators of the campaign have created an app which is, in essence, a simple <iframe> that displays a fraudulent version of Facebook’s login page. Cybercriminals are abusing the Facebook application platform to carry out phishing campaigns against users which appear legitimate thanks to the fraudulent use of Facebook's own Transport Layer Security (TLS) security certificates, a protocol used to help keep domains and user communication secure.
The phishing web site is hosted on hxxp://gator4207.hostgator.com/~labijuve/a2/, which leads to a identical yet fake copy of Facebook’s verification page. Despite the resemblance that the iframe bears to Facebook’s actual webpage, the differences between the two sites become obvious when they’re displayed next to one another.
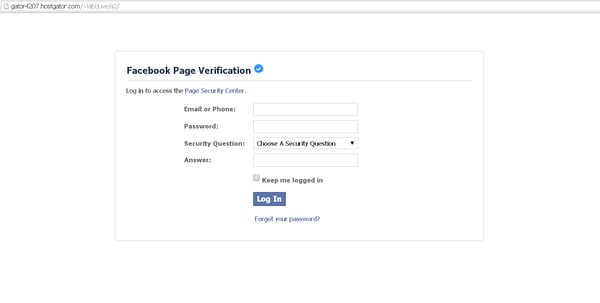
Fraudulent Facebook login page ready for victims to log in.
To make the trick work, cybercriminals use Facebook’s app platform and with that they can display the phishing page under the legitimate Facebook domain and Transport Layer Security (TLS) certificate. To avoid HTTPS browser warnings, they also use HTTPS on the phishing site.
The site’s source code reveals that the phishing site is really just a simple call to action form. In this case, users fall victim to how they interact with the fake login form on the site.
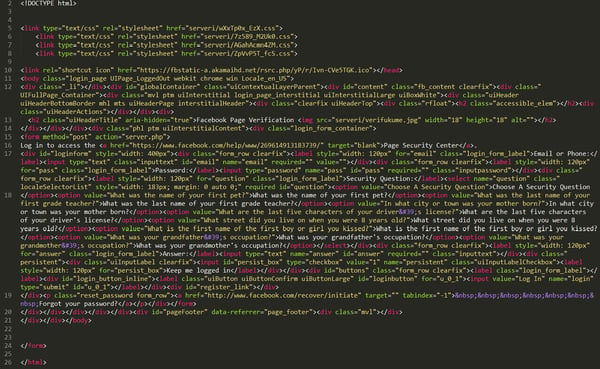
Form is calling "server.php" and “server1.php”

Extended JavaScript code (pgfl4Qozb5l.js) is not used -- only HTML with CSS
Creating a veil of trustworthiness
Despite the trustworthy environment that the attackers have taken the time to prepare, it could still come across as suspicious to tech-savvy users. To eliminate that feeling for those users, the site’s creators implemented one trick that manifests while the user enters personal credentials. When the user enters their name, password and answer to a security question, the form automatically denies the credential and tells the user that they were entered incorrectly.
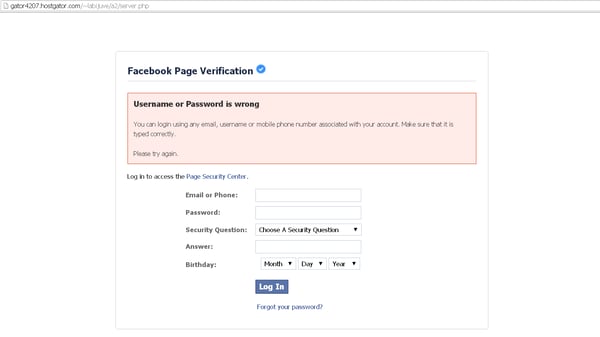
The site pretends that the user’s submitted credentials are incorrect.
Once the user enters the credentials a second time, the form acts as if the credentials were entered correctly, while in fact, they were directly sent to the attacker’s email account. After the credentials have been entered a second time, the victim is told to wait up to 24 hours for the submission to be approved.
This time can be used in various ways --the attacker can access the compromised account themselves, or they can sell it to others who can use it to spam or scam other users. It’s common to use hijacked accounts to lure the victim’s friends to the phishing page or to ask them for some money donation or other information.
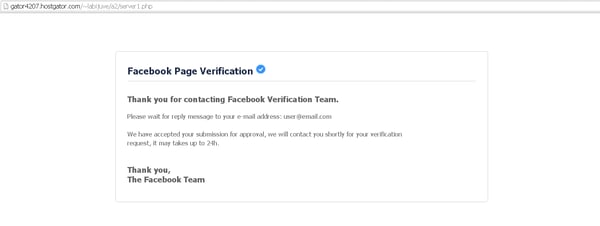
Last message displayed to the victim describing an email that will, unfortunately, never arrive.
Although this type of ‘fresh phishing’ scam is unfortunate, Facebook is already prepared for similar situations and has some features that can reveal attempted attacks.
Don’t overlook your security settings on Facebook
Your best bet for staying protected from these kinds of cyberattacks is to make use of Facebook's two-step verification process. The Login Approvals feature keeps your account from being immediately compromised if it falls into the wrong hands, and it will also alert you when someone is attempting to gain access to your account.