Didn't really understand how Elliot plans to hack the FBI in episode eps2.3_logic_b0mb.hc? Avast explains!
Finally! Elliot is back to his old ways, hacking and being a vigilante.
The episode began with Elliot speaking out loud about his plan to hack the FBI. Darlene tries to convince Angela into helping with the FBI hack and she succeeds, something Elliot will not be happy about. The FBI in the meantime, is conducting a full on investigation at E Corp and then travels to China to visit back-up sites and to access the encrypted E Corp servers, in addition to wanting to view all of China’s intelligence on the Dark Army.
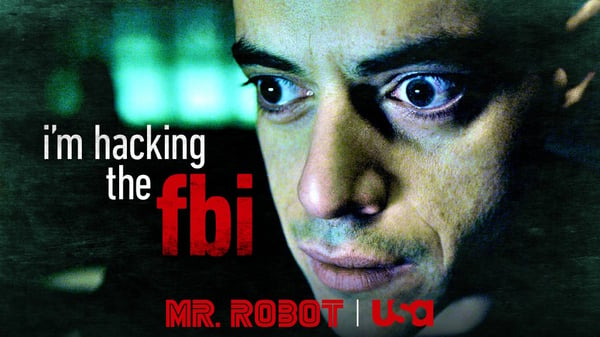
Image via: USA Network
We gained more insight into the characters of the show in this episode. White Rose, does not have a sister and oh yea, he is China’s Minister of State Security! We learned that Joanna is just as ruthless as her still missing husband, ordering to have Kareem murdered and even somehow trying to justify keeping alive for a few minutes before having him shot. Ray runs a dark and nasty online black market, which was a bit expected.
The theory that Elliot is living in an institution still seems to be very true. Angela tells him about how she thinks she is overfeeding his fish. If Elliot were really living with his mom he should have been able to take his fish with him. I highly doubt she is allergic to small, pet fish… Angela and Darlene, like all of Elliot’s visitors, speak with him at the “dining room table” and RT logins into the Kali system with the username “caregiver”, which is probably what Ray is for Elliot.
I sat down with my colleagues Michal and Jaromir to discuss the hacks and other parts of the episode to find out how realistic they are.
In the opening scene, Elliot explains how he is going to hack the FBI. Step one, identify the target and its flaws. Step two, build malware and prepare an attack. Step three, a reverse shell two-stage exploit the ideal package - load the malware into a femtocell delivery system, his personal cell tower that will intercept all mobile data. Step four, write the script. Final step, launch the attack. Once he does, he will own the Android phone of every FBI agent in that network, domain admin.
Stefanie: Considering the fact that we haven’t seen Elliot sit in front of a terminal yet this season, he sure made up for it by explaining his plan to hack the FBI. In step one, he says he has identified his target and it’s flaws. In this case, his target is the FBI’s standard issued Android devices and its flaws are the zero days he will use against them.
Are Android devices perhaps more vulnerable than other operating systems? Do Android devices often have vulnerabilities that can be exploited and what can users do to protect themselves?
Jaromir Horejsi, senior malware analyst: Yes, Android devices are more vulnerable, because of the big fragmentation of market. There are many different hardware manufacturers, producing different devices with different versions of the operating system, so there is a higher chance of bugs slipping in during development. The second reason is that so many people use Android devices, so there is a higher reward for hunting for vulnerabilities, because the exploit pool is much larger. Some of the bigger Android vulnerabilities were Metaphor and Stagefright. Users should definitely update their Android operating system whenever an update it made available. Companies push updates that often include patches to fix vulnerabilities or bugs.
Stefanie: In step three, he mentions a reverse shell and a two-stage exploit. What is a reverse shell and what is a two-stage exploit?
Jaromir: A reverse shell is where you attack the victim’s device and on the device a "reverse shell" program is executed. This program will connect the device back to the attacker’s machine, giving the attacker “shell” also known as administrator access -- full control of the device. A two stage exploit: exploits usually have one or more encryption stages, which first decrypt the shellcode itself and the last stage is executing the shellcode.
Stefanie: Step three also includes loading malware into a femtocell delivery system that will intercept all mobile data. What is a femtocell delivery system?
Jaromir: Normally, you have a big base transceiver station (BTS) towers, which are cover an area with mobile network coverage. These towers are huge and femtocells are smaller cellphone towers that amplify coverage in areas that lack coverage. Femtocells connect via broadband and provide cellular signal. Elliot will probably intercept data going through the femtocell. Femtocells can be purchased online and if you have a bit of technical knowledge, you can update the firmware and use it for Man-in-the-Middle attacks.
Stefanie: Darlene was probably referring to the femtocell then, when she told Angela that all she had to do is drop a small device in the E Corp office.
Angela meets her ex-boyfriend, Oliver, at a bar. He, in a very obvious way, tries to slip in a question about the CD that was used to set off the E Corp takedown mission into their conversation. Angela turns his phone around and sees that he had been recording their conversation and drops his phone into a glass of beer.
Stefanie: Do you think this really got rid of the recording and destroyed Oliver’s phone?
Michal Salat, threat intelligence manager: Oliver’s phone probably didn’t die when Angela dunked it into her glass of beer - it was in there for too short of a time. Some of the parts may stop working, like microphone and speakers, but he should be able to recover the data.
In the one of the last scenes, we see Elliot log into Ray’s online business - a black market selling weapons, trafficked women and drugs.
Stefanie: I am afraid to ask, but do these kinds of sites really exist online?
Michal: Unfortunately, yes. They exist on what is known as the darknet. The darknet can be accessed via Tor networks and often these sites require accounts, just as Ray’s site does. The items sold on the darknet are sold for Bitcoins, as to not leave a trace.
What did you guys think of the episode? Let us know in the comments below!