Avast introduces a new decryption tool that will help Mac users infected with the FindZip ransomware decrypt their files.
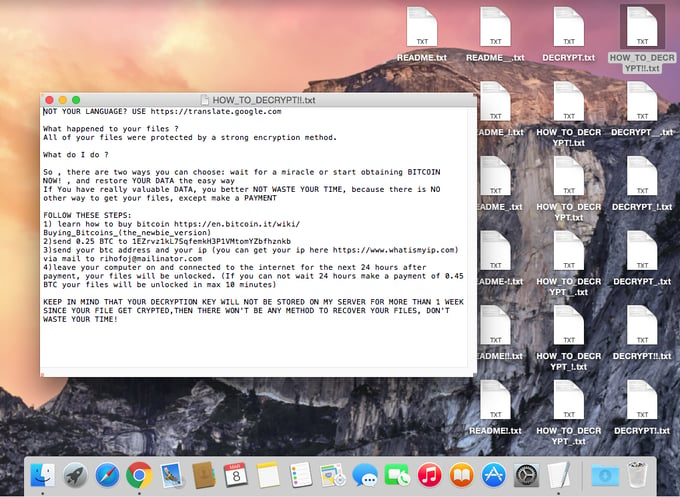
Late February 2017, a new type of ransomware for Mac was discovered. This ransomware, called FindZip, infects users by pretending to be a cracked version of commercial applications, such as Adobe Premiere Pro. Once it infects a Mac, it utilizes a ZIP encryption to encrypt documents - the exact same scheme used by the Windows ransomware, Bart, which we decrypted last summer.
MalwareBytes already published a technical analysis of FindZip, as well as a description of the decryption process. However, because the instructions described by MalwareBytes may be complicated for some, we created a more user friendly decryption application.
The FindZip decryption tool is available on our free ransomware decryption tools page, along with all of our ransomware decryption tools.
Running the ransomware decryptor on Windows
If you decide to copy your encrypted files from your Mac to a Windows system, using our decryptor should be straightforward, and you won’t need to install any other software.
Running the ransomware decryptor on Mac
As the ransomware decryptors released by Avast are Windows applications, Mac users (and Linux users) need to install an emulation layer for the Windows application. The decryptor was tested with CrossOver and Wine, other emulation programs might work as well though.
This guide describes how to run the decryptor tool using Wine for Mac. The decryptor tool was tested on MacOS 10.10 (Yosemite) and 10.12 (Sierra).
Installing XQuartz
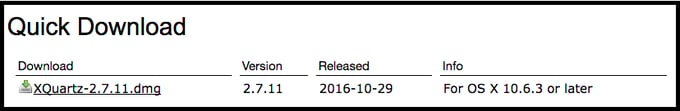
You first need to install a windowing system for your Mac. Go to https://www.xquartz.org (or Google “XQuartz for Mac”) and download the DMG installation file.
If the downloaded file doesn’t open automatically, open it from your Downloads folder.
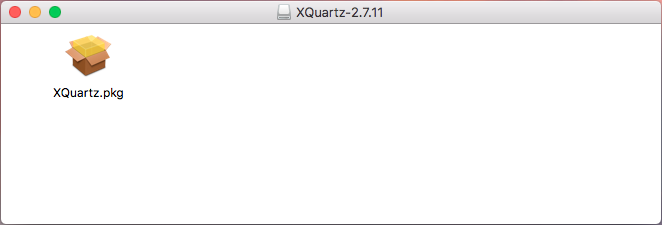
Double-click on the “Quartz.pkg” icon and the installer should open.
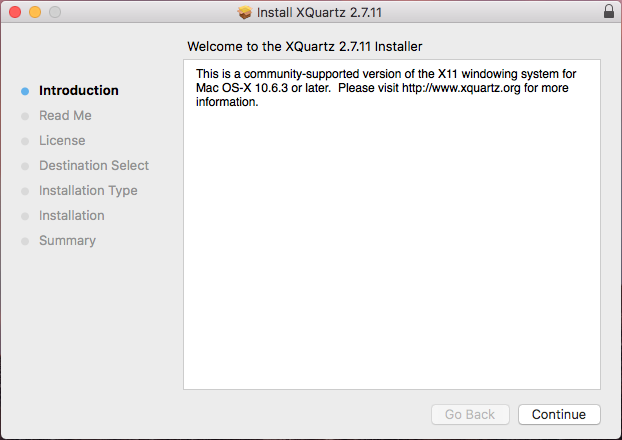
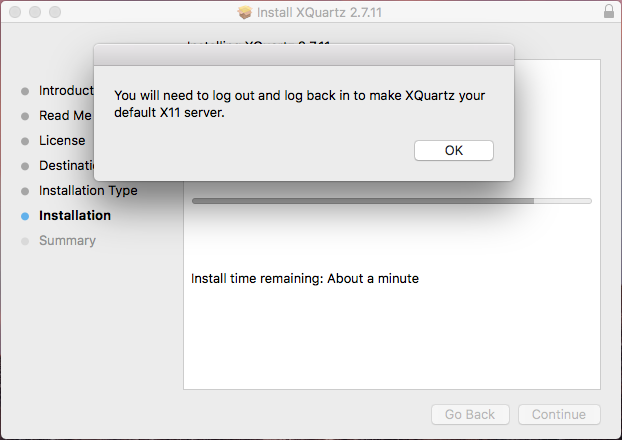
Keep clicking “Continue” or “Install”. You may be prompted to agree to the license and enter your password to install a new application. The installation process can take a few minutes. During the installation, you may be prompted to log out and log back in to complete the process:
Note: if you skipped installing XQuartz and went straight to installing Wine, it will probably complain that you need to install XQuartz first :)
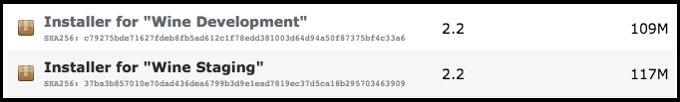
Installing Wine
Go to https://wiki.winehq.org/MacOS (or Google for “Wine for Mac”, not just “wine” ;-) ) and follow the link to download the PKG packages. Download the “Installer for Wine Staging”:
After downloading, you can find it in your Downloads folder:
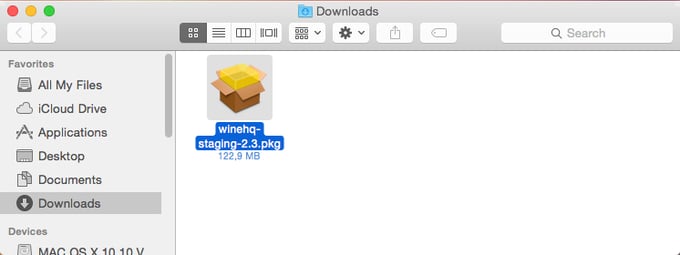
Run the installer by double-clicking on the icon:
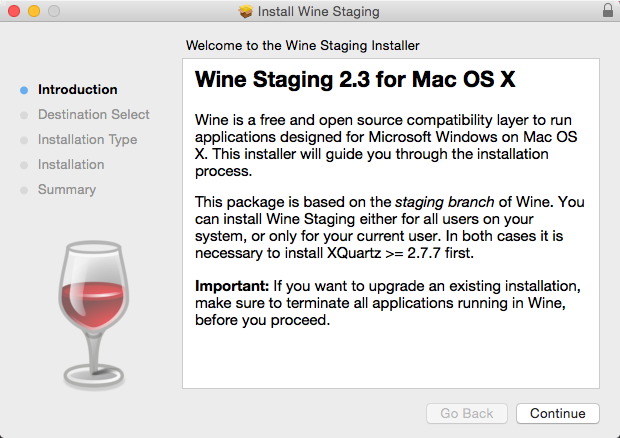
Click “Continue” and select “Install for all users on this computer”. Then keep clicking “Continue” and “Install”. You may be prompted to enter your password, as you are installing a new application. When the installation is complete, click “Close”.
You may now download the Avast decryptor and run it seamlessly.
Important note: If you already had Wine installed prior to being infected with the ransomware, the entire Wine configuration is probably encrypted. In that case, you need to delete the folder \Users\<YourUserName>\.wine before running the decryptor application.
Running the decryption application
To run the decryptor, download it from our Avast free decryptor tools page and double-click on the application icon:

It will take some time for the first-run configuration.
- If you are prompted to install “Mono”, click “Cancel”
- If you are prompted to install Gecko, press “Install” and let the installer download and install it.
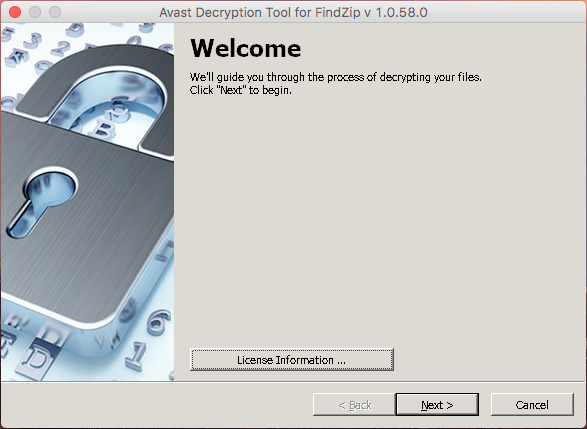
When the initial configuration is complete, the decryptor will run and show the “Welcome” screen:
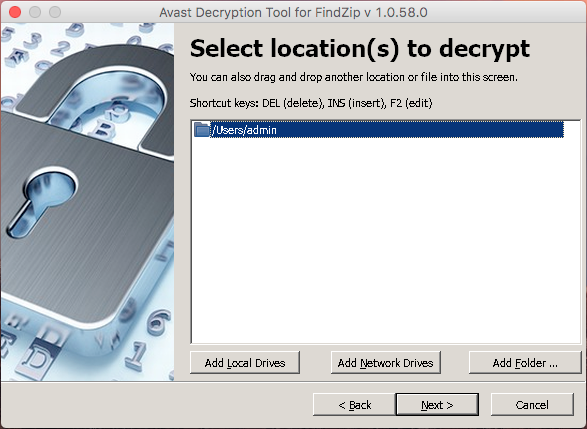
On the next window (after clicking “Next”), you can select one or more locations, where the decrypted files are. By default, this contains the name of the current user’s home folder:
The default setting is usually fine. Press “Next”. Then, you need to enter a pair of original/encrypted files. You can either drag and drop from the Mac folders, or can browse for the file by clicking the “…” button.
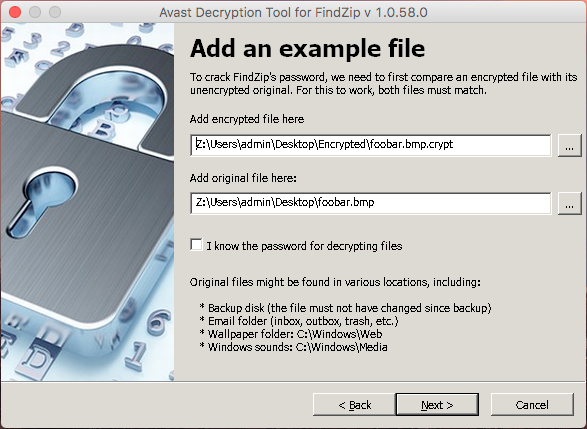
Once both files are entered, click “Next”.
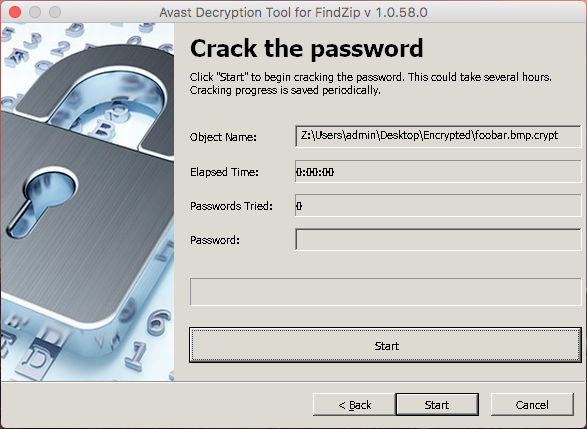
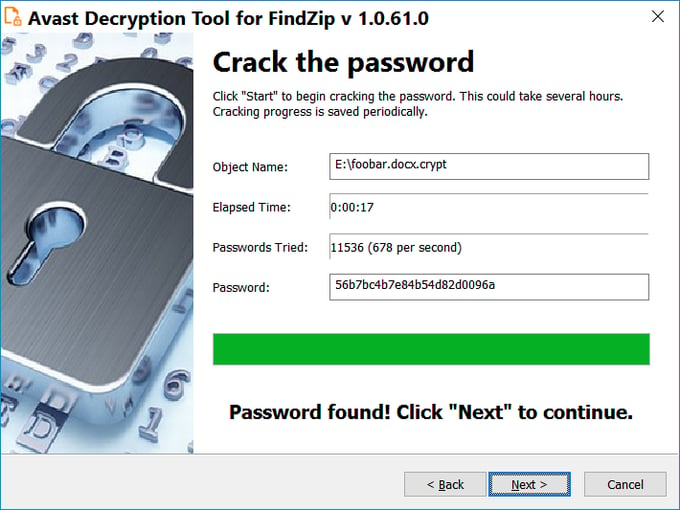
On this screen, the password cracking process is done. Click “Start“ and wait until the decryptor finds the password. It usually takes about a minute to crack the password for files encrypted by FindZip.
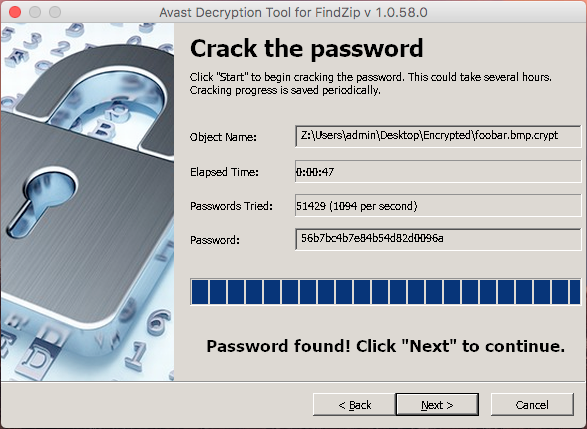
When the password cracking process is done, press “Next“.
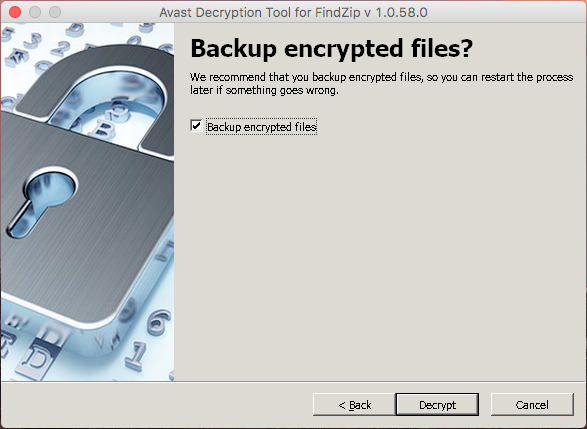
On the final screen, you can opt-out from creating backup copies during the decryption process. It is not recommended to do so, however.
After clicking “Decrypt”, the application will decrypt all the files in the folder that were entered in the “Select location(s) to decrypt” screen.
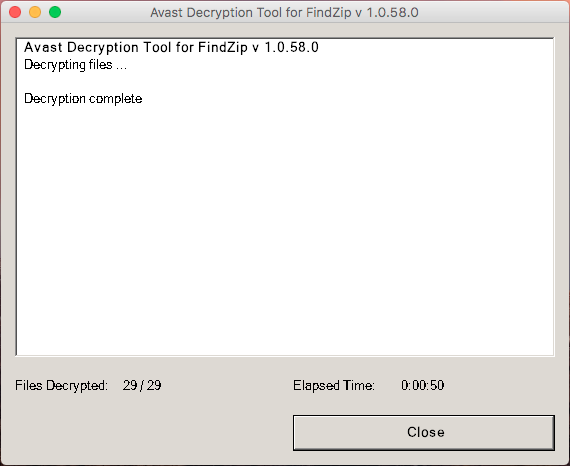
When the decryption is done, just press “Close” - and that’s it! Your files will be decrypted!
Special thanks
We would like to thank Peter Conrad, the author of PkCrack, who granted us permission to use his library in our decryptors. Furthermore, a special thanks also goes to my colleague, Ladislav Zezula, for preparing this decryptor.
IOCs
c68814901d0af5de410c152e62a06a51c16ec7fe118f1e5251bbcdbb27364709
d19b903adbd0f8c119d0d8f25b194bdd24b737357a517f23ca5cdc6c75b35038