The Avast Guide to Android Apps Part 1: This guide teaches you how to identify malicious apps and keep them off your Android phone.
By now, you should be familiar with that sudden bout of uncertainty as you are gearing up to install a new application. How do you check if an Android app is safe to install? Does it have a virus? What does a malware app even look like? If you have ever felt threatened at the prospect of installing a fake app masquerading as a fan-favorite, then this guide is for you.
From malware to overheating and more, smartphones today suffer from the same issues PCs do. In this four-part guide, we reveal every threat you and your trusty sidekick can face, and how to outsmart them.
In Part 1, we discuss all the common malware that can infect an Android smartphone and how to deal with it. Part 2 delves deeper into virus infections, and Part 3 deals with overheating issues. Finally, in Part 4 we reveal how to manage your app permissions such that no one can ever see that hidden folder on your phone. Ever.
Let’s begin by filling you in on the tell-tale signs of a malicious app.
Malware? On a phone? Really?
Often disguised as legit applications, mobile malware can spy on user activity, steal sensitive data such as credit card/bank details, and send that data to third parties. Chief culprits found here include…
- Spyware: These are apps designed to secretly gather information on a user, all the while posing as something helpful. Spyware is often disguised as games to tantalize the user into installing them. No sooner are they installed than sensitive information such as contacts, user habits, chat records, and device details are being sent to cybercriminals.

- Trojans: Much like their namesake, trojans hide inside legitimate apps and trick users into installing them. Trojans can simply be annoying by sending texts and hijacking browsers, or they can be more destructive by stealing your banking details and taking over your device.

- Phishing: Phishing is the practice of misleading users to download malware or give away information under false pretenses. The sender pretends to be from a reputable source and uses social engineering techniques to pressure the user into opening an infected attachment or clicking on a malicious link. Since mobile screens are small, they make lucrative targets for phishing schemes as the imperfections aren’t as noticeable.
Google has its own anti-malware solutions in the form of built-in protection on Android devices and Google Play Protect. The latest Android version called Pie also has very robust security features which disable camera and mic for background apps and compiler-level security for detecting dangerous app behaviors.
While these technologies are quite powerful, they have no rule over the permissions you may grant (perhaps unwittingly) to other apps. In other words, it’s best you know what to look for if you want to ensure there are no unsavory surprises waiting in store.
So, how can you make sure that really interesting new app isn’t going to infect your device? Here are a few ways to find out…
Fake apps — the red flags
Even though some can be cleverly designed, the vast majority of fake apps are quite easy to spot if you look at it the right way. Keep the following in mind...
- Check for typos in the app title and description — Legit developers will probably be well aware that their product description is one of their bigger marketing assets. Not-so-legitimate developers on the other hand often play fast and loose with their descriptions. They will also spoof the names of real developers, so check for that, too.
- Read the reviews — Well established apps usually have well thought-out reviews, some good, others bad. If an app’s review section looks too good to be true (i.e. all 5 stars and blazingly good words), then chances are it is. Furthermore, since developers can’t delete a review, someone just might leave a warning note for other curious users on the verge of installing that app.

- Look at download stats — If that really popular app has next to no downloads, then it’s most likely a fake. Likewise, poor download statistics can also mean the app is being ignored intentionally. Look towards the bottom of the product listing in the Google Play Store for this information.

- Look at permissions — Best seen as the EULA equivalent of an app store, user permissions are glossed over all too quickly. But this can sometimes lead to handing over device control to unwanted agents. Spend the extra 10 seconds to go through that permission list before hitting install. It’s more than worth it.
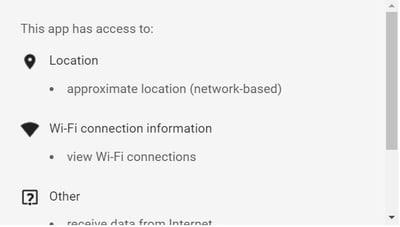
Click on “view details” under app permissions
before installing to see what the app
needs access to. If something does not
seem right, don’t install the app.
- Check out the developer — If the name of the developer is clearly a rip-off, then it’s best to avoid anything from them. Likewise, check to see what other apps they offer and repeat the exercises mentioned above for all of them.
- Google every app you intend to download — While it may seem like an added step, you will thank us later. Just copy the title and append it with words like “review” or “scam” to see what the word on the street is.
Dealing with the worst case scenario
Red alert! Your failsafes have failed and your phone is staring into the abyss! Fear not, we’ve got you covered. Consider the following steps to get your phone back up and running in no time…
- Clear the app’s cache and data — An app’s cache is where it temporarily stores all data that it needs to work. First order of business upon discovering a malicious app is to make sure it has no compromising information. Go over to Settings > Installed Apps > Suspicious App > then click Clear Cache. It’s also a good idea to clear the app data while you’re at it.
- Check permissions — In an attempt to get as much of your information as possible, malicious apps will try to get you to give them all sorts of useless permissions. Simply go to Settings > Apps > Suspicious App > App Permissions and make sure they’re at your comfort level.
- Delete the app — If you are even a little bit suspicious, it’s better to be safe by shooting first, asking questions later. Oftentimes, people simply disable an app by swiping it up, thinking they have uninstalled it. To make sure, go to Settings > Installed Apps and permanently delete the app from there.
- Take your phone to the service center — If you continue facing issues even after deleting an app, it might be time to take your phone to the provider for a more thorough evaluation.
- Do a factory reset — You can just hard-reset your phone to its original setting by going to Settings > Backup & Reset > Reset. You will need to enter your passcode to carry on. Remember, a factory reset will delete all your apps and data, which is why it’s always a good idea to regularly backup your whole system.
Mobile security for Android
Always remember you have the option to call in reinforcements to secure your front lines. There is no shortage of mobile cybersecurity suites on the market, but make sure you vett the product before you purchase. There would be no greater irony than for you to install what you think is cybersecurity, when in reality the program only causes more harm. Third-party labs like AV-Comparatives and AV-TEST independently examine and compare cybersecurity products. Look at their reviews and results before committing to a brand.
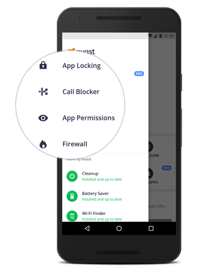
Our own solution, Avast Mobile Security for Android, is free to install and offers the following safety-ensuring features:
- Secure connections — Protect your payments, your photos, and your data everywhere you go.
- Safe browsing — Avast antivirus tech keeps all your web browsing sessions malware-free.
- Privacy control — With app locking, call blocking, clear permissions, and a user-friendly firewall, you can configure the level of security precisely to where you’re comfortable.
Stay vigilant
With Android Pie, Google is bringing its most advanced AI and machine learning technologies to the consumer front, which will no doubt add a whole new layer of security to your smartphone.
But, as mentioned above, most malware apps target user inattention as their entry choice. Simply put, they are counting on your ignorance and complacency. If you willingly give permission to an app to access your mobile device, then there is little that Google, or any other software-maker, can do.
Practicing due diligence is your only defense against such apps. For the most part, safety boils down to a good dose of healthy suspicion and a little bit of patience.
Next week in The Avast Guide to Android Apps — All hell has broken loose! Your phone has a virus, and you’re one wrong move away from losing all your selfies! Or, have you already lost them? What should you do? Stay tuned...