Malicious landing pages infected routers, sending users to phishing pages posing as banking sites and Netflix
In late November the Avast Threat Labs team discovered cyberattacks that exploited Brazilian users’ routers to send them to phishing pages designed to look like actual websites the victim wanted to visit. In this case, sites included Brazilian banking, and news sites, as well as Netflix.
The sites were:
- bradesco.com.br
- santandernetibe.com.br
- pagseguro.com.br
- terra.com.br
- uol.com.br
- Netflix.com
Online banking sites and sites like Netflix are often targeted by cybercriminals in such hijack attacks, as it allows them to easily steal valuable login credentials.
This type of router attack is typically initiated when the user visits a compromised website with malicious advertising (malvertising), which is served using third-party ad networks to the site. In this case, users were automatically redirected to one of two router exploit kit landing pages initiating the attack on their router, without user interaction, in the background. Their routers then redirected them from real business pages to lookalike phishing sites. The Avast Web Shield blocked two malicious websites infecting users’ routers nearly 5,500 on Nov. 25, followed by more than 1,000 blocked URLs the following day.
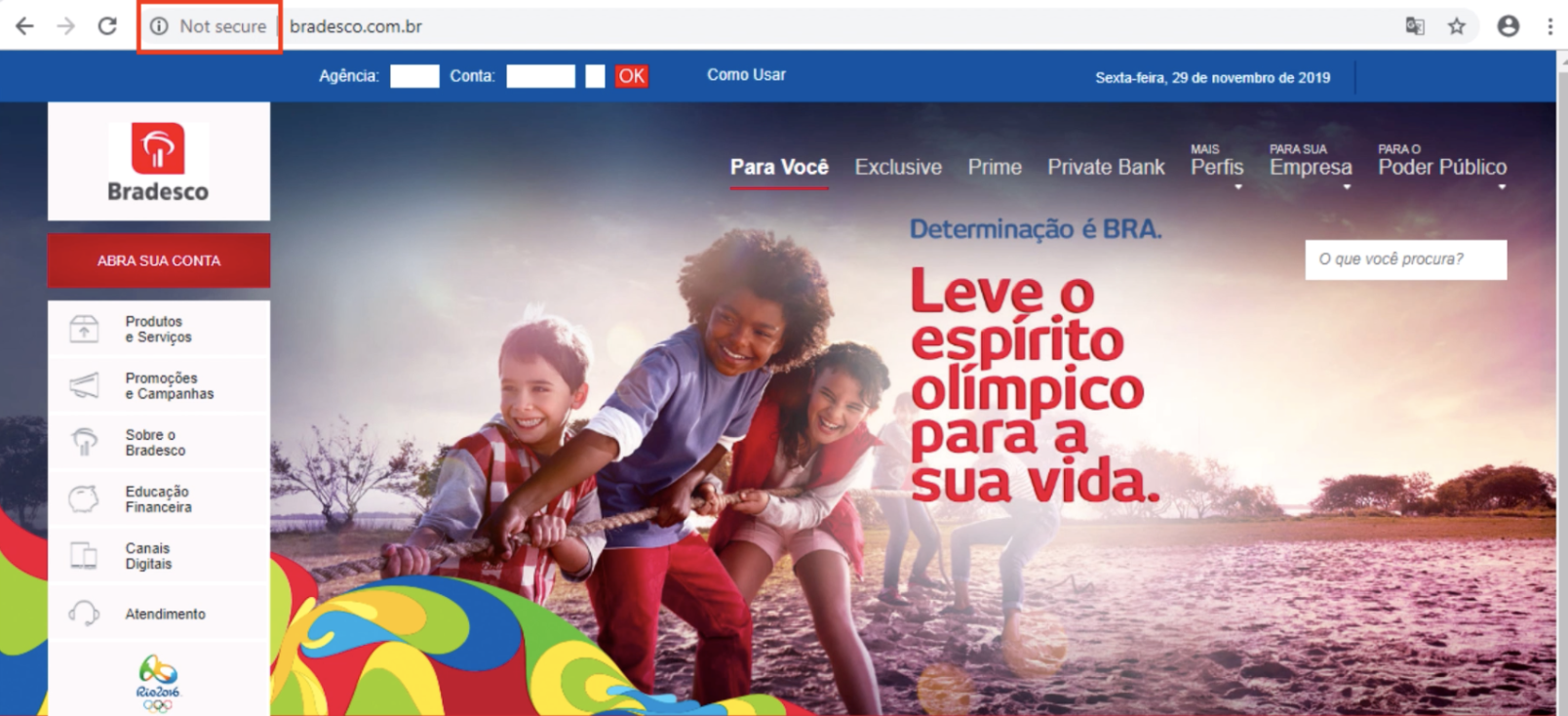
The team visited the phishing version of the Banco Bradesco site, which victims of the router attacks were redirected to when trying to visit the bank’s website. The address bar on the site revealed the site was not a secure HTTPS site, which would have shown the padlock symbol. An error message also showed the site to be unsecured. Most of the links on the site don’t work. The login page does work, however, in the sense that the victim can log in to their account by filling in their credentials at the top of the page.
The phishing site does not validate the login credentials, it has no way of doing so, so it just automatically pretends to log the user into their account. The phony site thus captures visitors’ usernames and passwords, and subsequently displays a pop-up message notifying the user the system is temporarily unavailable and to try again in a few minutes. This campaign is no longer active.
To prevent a DNS hijack attack:
- Update your router’s admin credentials with a strong password.
- Update router firmware to the latest version. You can typically find this on the router manufacturer’s website.
- Change your login credentials, especially for your online banking services and router, using strong passwords.
- Make sure to check if your banking website has a valid certificate, by looking for the padlock in the URL address bar of your browser.
The Avast Web Shield feature, included in both the free and premium version of Avast Antivirus proactively protects users against router CSRF attacks. Avast Wi-Fi inspector, part of the Avast Free Antivirus and premium consumer security software products, can also evaluate the strength of your router password, test the network for DNS hijack issues and show a list of hijacked domains. Download Avast Free Antivirus today and enjoy comprehensive security and protection.
Read more about the Avast Threat Labs investigation of the GhostDNS Exploit Kit on the team’s Decoded Blog.