This post was updated Tuesday, July 23, to add that an eighth stalkerware app, this one from a different developer, was reported by Avast and removed by Google’s Play Store.
Mobile threat researchers at Avast have detected eight apps on the Google Play Store that allow people to stalk employees, romantic partners, or kids. After Avast reported the apps to Google, the company removed them from its app store.
Avast reported seven of the apps to Google last week, and have subsequently detected an eighth app from a different developer that takes privacy violations even further. It, too, has now been removed.
The eighth app, Family Employee Monitor (Enterprise Tracking), bills itself as an app for parents to monitor their children, or organizations to manage employees. The Avast Threat Labs is classifying this as stalkerware/surveillance software because it can access and exfiltrate social media activity of the end-user on Facebook, Messenger, Kik, Skype, Hangouts, among other chat platforms.
The apps have been installed a combined 140,000 times, with the most-installed apps being Spy Tracker, and SMS Tracker, both with more than 50,000 installs.
The apps require the snoop to have access to the phone they want to spy on. The snoop can download the apps from the Google Play Store and install them on the target device. The app then prompts the person who installed the app to enter their email address and password. The spying app is sent there.
The apps also help the snoop to hide the surveillance by providing directions to uninstall anything noticeable to the phone’s owner. Upon setup there is no app icon, so the targeted person does not see any sign of the stalkerware app installed on their phone.
The apps are able to track the surveilled person’s location, collect their contacts, SMS and call history.
The apps were published under the following names:
- Track Employees Check Work Phone Online Spy Free
- Spy Kids Tracker
- Phone Cell Tracker
- Mobile Tracking
- Spy Tracker
- SMS Tracker
- Employee Work Spy
- Family Employee Monitor
Nikolaos Chrysaidos, Avast’s head of mobile threat intelligence and security, identified the apps using Avast’s mobile threat detection platform apklab.io.
“These apps are highly unethical and problematic for people’s privacy and shouldn’t be on the Google Play Store,” Chrysaidos said. “They promote criminal behavior, and can be abused by employers, stalkers or abusive partners to spy on their victims. We classify such apps as stalkerware, and using apklab.io we can identify such apps quickly, and collaborate with Google to get them removed.”
Below are excerpts from the descriptions of three of the apps from the Google Play Store:
SMS Tracker – Apps on Google Play
“Our app will help you monitor work time of your employees to save time and save money. Notify the users of work phones that you are going to install the app. It will teach your employees to use their time at work wisely, to reduce time spent on messengers and arrive to work in time.”
Spy Tracker - Apps on Google Play
“Find out more about your child’s life, interests, friends and plans. Parents are responsible for every step that their kids make. So this app is created to monitor them and protect them from dangers that can be revealed via cell phone. It is better to talk to children, but if you are not a good listener…”
Employee Work Spy - Apps on Google Play
“Finding a skilled employee is only half a task. The biggest challenge is to keep him faithful to the company and its mission. A lot of employees may be just skipping work during work hours. People usually spy on kids, but employees need a strict control too.”
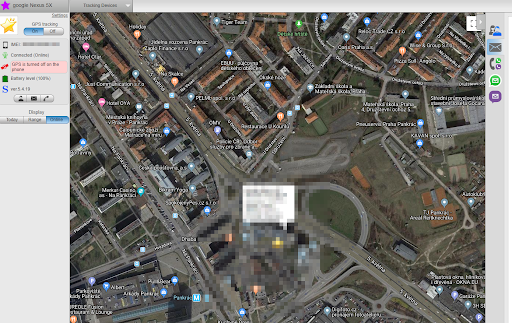 The spy apps allow snoops to find their victim’s location.
The spy apps allow snoops to find their victim’s location.
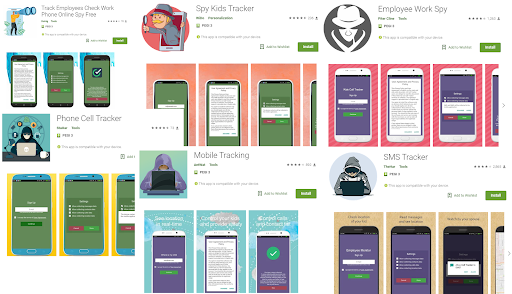 Stalker apps in the Google Play store.
Stalker apps in the Google Play store.