GM Bot has targeted hundreds of thousands of mobile users in the last quarter.
A variant of the Android banking Trojan GM Bot is now targeting customers of more than 50 banks around the world, including Citibank, ING, and Bank of America. In the latter half of 2016, our mobile users encountered GM bot more than 200,000 times.
GM Bot – also known as Acecard, SlemBunk, or Bankosy – scams people into giving up their banking log-in credentials and other personal data by displaying overlays that look nearly identical to banking apps’ log-in pages. Subsequently, the malware intercepts SMS to obtain two-factor authentication PINs, giving cybercriminals full access to bank accounts.
GM Bot’s code is open source in the sense that it is freely available on the darknet, meaning anyone can distribute it and build upon the code.
What exactly is GM Bot?
In a nutshell, GM Bot is mobile banking malware that can gain full administrative rights of a device, and thus can intercept SMS and display overlays to steal valuable information.
GM Bot first appeared on Russian darknet forums in 2014. Since then, its source code has leaked and a second version has been developed by its original creator, GanjaMan.
How GM Bot works
GM Bot is a Trojan that looks like a harmless app on the surface, but is actually malicious. It is mostly distributed on third party app stores that don’t have strict security checks like the Apple App Store or the Google Play Store do. GM Bot often disguises itself as an adult content app or a plug in app, like Flash.
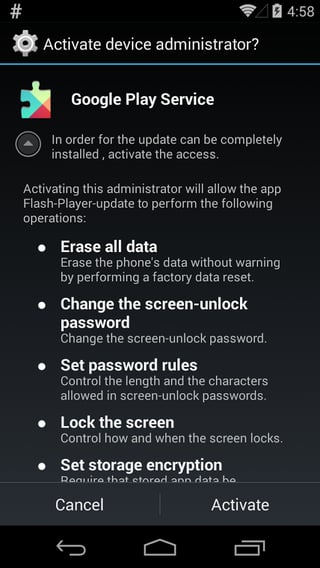
Once downloaded, the app’s icon disappears from the device’s home screen, but that doesn’t mean the malware has disappeared from the device. The app persistently requests administrative rights. If granted these rights, the malware can cause serious damage.
With full administrative rights, GM Bot knows and can control everything happening on an infected device. The malware springs into action when an app from its list, which mainly consists of banking apps, is opened. A list of banks a GM Bot variant is currently imitating can be found below.
When an app targeted by GM Bot is opened, the malware can display an overlay, which is a page on top of the one you should be seeing, that looks very similar like to the app you have open. You will be able to enter your login credentials into the overlay, thinking you are logging into your banking app, only your credentials aren’t being sent to your bank’s servers – the information is being sent to cybercriminals. This social engineering technique is used to deceive users into giving up personal and sensitive information.

Even worse, since GM Bot can intercept SMS, and its bots can steal your two-factor authentication PIN to complete a transaction without your realizing it. That’s right, cybercriminals can get around that extra layer of security you have set up if you aren’t careful!
The malware can send information like CCV number, code taken from SMS, phone numbers, card numbers, etc., back to its command and control (C&C) servers.

GM Bot is evolving
GM Bot’s source code was leaked in late December 2015, so it is now available to everyone, so just about anyone with a bit of tech knowledge can distribute the malware. Cybercrooks can go a step further and tweak GM Bot’s code, customizing it to gather more information. This means that new variants with new and different capabilities are constantly being created.
We have seen a significant rise in the number of GM Bot samples since its code was leaked. Our friends at McAfee, for example, have found variants of GM Bot whose overlay request users scan the front and back side of their identification card.
I took a deeper look at the sample McAfee analyzed and discovered that the following banks and services across the world are imitated by the GM Bot variant:
USA and Canada
American Express
BNC
Chase
CIBC
Citi Bank
ClairMail
Coinbase
Credit Karma
Discover
goDough
First PREMIER bank
Bank of America
JPMorgan Chase
Skrill
Western Union
PayPal
PNC
SunTrust
TD Bank
TransferWise
Union Bank
USAA
US Bank Access Online Mobile
Wells Fargo
Austria
BAWAG P.S.K.
easybank
ErsteBank/Sparkasse
Volksbank
Bank Austria
Raiffeisen
Australia
Bank West
ING Direct
National Australia Bank
Commonwealth Bank
Bank of South Australia
St. George Bank
Westpac
Germany
Deutsche Bank
ING DiBa
DKB
Sparkasse
Comdirect
Commerzbank
Consorsbank
Volksbank Raiffeisen
Postbank
Santander
France
ING Direct
Crédit Mutuel de Bretagne
Crédit Mutuel Sud Ouest
Boursorama Banque
Téléchargements
Caisse d'Epargne
CIC
Crédit Mutuel
La Banque Postale
Groupama
MACIF
Crédit du Nord
Axa
Banque Populaire
Crédit Agricole
LCL
Société Générale
BNP Paribas
Poland
Comarch
Getin Group
Citi Bank
Bank Pekao
Raiffeisen
BZWBK24
Eurobank
ING Bank
mbank
IKO
Bank Millennium
Turkey
Akbank Direkt
QNB Finansbank Cep Şubesi
Garant
İşCep
Halkbank
VakıfBank
Yapı ve Kredi Bankası
Ziraat
How to protect yourself
Install an antivirus app, like Avast Mobile Security. A good antivirus app will detect and block malware, like GM Bot, before it can infect your device.
Stick to trusted sources, like the Google Play Store and the Apple App Store. While third party app markets may offer apps that cannot be found on trusted sources or may offer premium apps for free, their offers can be too good to be true. As mentioned above, most third party app stores don’t check the security of the apps being uploaded.
Be careful which apps you give administrative rights to. Administrative rights are powerful and give an app and whoever is behind it full control of your device.
Android:Banker-MQ[Trj]
E5DF30B41B0C50594C2B77C1D5D6916A9CE925F792C563F692426C2D50AA2524