What is a VPN?
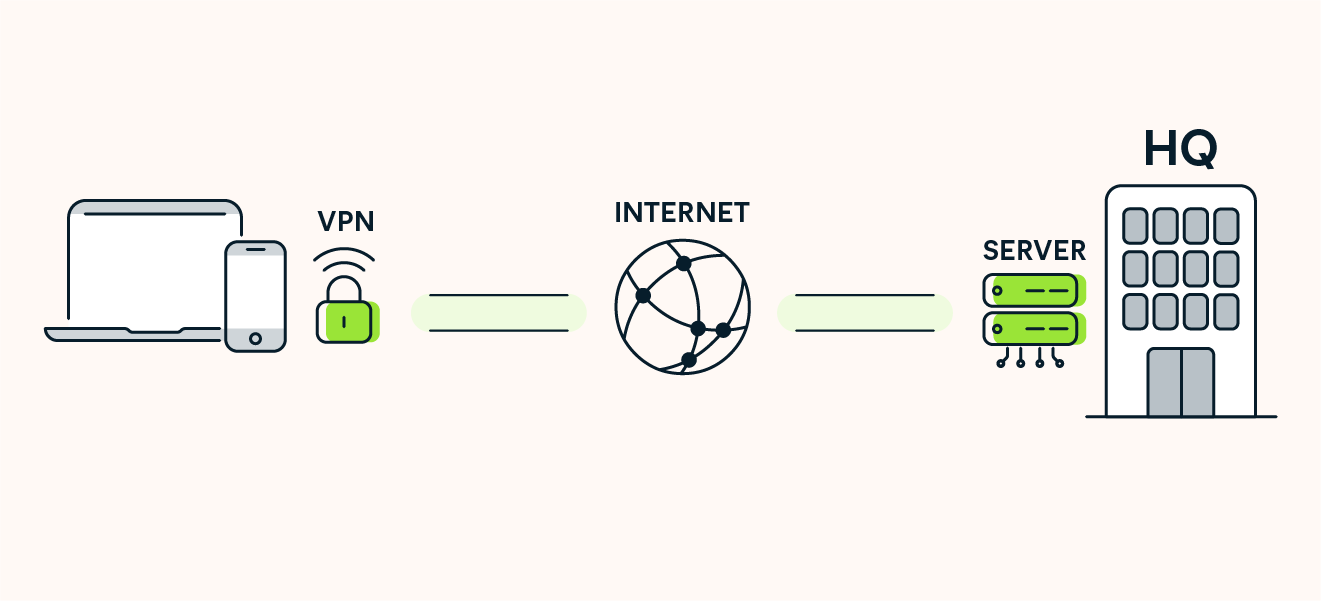
A VPN, which stands for "virtual private network,” is an app or service that encrypts the connection between your device and the internet, routing the data you send and receive through a secure VPN server.
Imagine the internet as a kind of highway that you explore on a motorcycle. You visit your favorite locations (websites), make purchases in shops, check out financial accounts, read the news, and play games. Sitting on a motorcycle, you’re completely visible. Anyone can peek into your private life along these digital highways. It’s easy to see your identity, view your online activity, and even follow you home.
With a virtual private network, instead of having your online activity exposed on the wide-open internet highway, all your traffic is routed through an encrypted, private tunnel that blocks others from seeing where you’re going or what you’re doing.
What does a VPN do?
A VPN creates a secure, encrypted tunnel through which data travels to and from your device and the internet, masking your IP address, changing your virtual location, anonymizing your online activity, and protecting sensitive data from hackers and snoops.
Here’s a closer look at what VPNs can do:
What does a VPN hide?
VPNs operate at the system level, encrypting and routing all online traffic through proxy servers. This masks your physical location and connection source, making it difficult for websites, hackers, or other third parties to identify or track you online.
When using a VPN, the following information is hidden:
-
Location and IP address
-
Recent searches (hidden from ISP)
-
Websites you’ve visited (hidden from ISP)
-
Data you send and receive
-
Files you download
But VPNs don’t hide or anonymize everything relating to your online activity. Some things that you do online can still be visible to to the websites you visit, including:
-
Activity on sites you’re logged into
-
Activity tracked by cookies
-
Device browser history
-
Browser fingerprinting and ad-tracking data
-
The simple fact you’re using a VPN
To boost your online privacy further, use a VPN along with a private browser, be selective about what sites you log into, and use a secure messaging app that’s end-to-end encrypted for sensitive communications.
Is a virtual private network safe to use?
A VPN is safe to use — as long it’s from a reputable VPN provider and used correctly. Trustworthy VPN providers are privacy-forward, with transparent security policies. An unsafe VPN provider may secretly track and log your online activity, have security vulnerabilities that lead to data leaks, or even sell your data to advertisers.
But although a VPN protects the privacy, security, and anonymity of your internet connection, you’re still at risk of malware and phishing attacks. So while it can reduce your exposure to hacking and online trackers, even the best VPNs are no substitute for top-rated antivirus.
For maximum safety, use other online security tools alongside an enhanced VPN like Avast SecureLine VPN, which boasts bank-grade encryption, a range of advanced security protocols, and a kill switch that acts as an ultimate fail-safe to help ensure unencrypted data isn’t exposed.
How does a VPN work?
VPNs work by routing a device’s internet connection via a specially configured remote server network administered by the VPN service. This means that all data shared across a VPN connection is not only encrypted but also masked behind a virtual IP address, allowing you to hide your identity and location.
Here’s how VPNs work in more detail:
-
A VPN connection is established: The user selects a server location and VPN protocol, and starts the connection through the VPN app on their device.
-
Outgoing data encryption: All outgoing internet data is scrambled, making it practically impossible to decode without the proper decryption keys.
-
Data encapsulation: The encrypted data is then wrapped inside additional data packets, further concealing its original purpose and making it harder to analyze or trace.
-
Secure tunneling: The data is transmitted through a protected tunnel to the VPN server, shielding it from surveillance or interception by hackers.
-
Decryption at the VPN server: Once the data reaches the VPN server, it’s decrypted, assigned a new virtual IP address, and forwarded to its intended destination.
-
Return path: For inbound data, the VPN repeats this process in reverse — encrypting, encapsulating, and securely tunneling it back to the user device, where it’s decrypted for the recipient to access.

How do encryption tunnels work?
VPN tunnels use cryptography to create secure pathways for data transmission, converting information into unreadable code and protecting it from unauthorized interception. This method shields both the content and metadata of your data, ensuring doubly enhanced privacy and security.
Different VPN providers offer varying degrees of encryption strength, but the best encryption software uses various methods to protect your privacy. Avast SecureLine VPN uses a combination of hashing, symmetric cryptography, and asymmetric cryptography for 256-bit AES encryption — the same standard that banks and the military rely on.
Avast also offers an extra layer of protection with our own DNS resolution system. The DNS (domain name system) is what translates numerical IP addresses into their more memorable text-based URLs. The DNS is what allows you to type in a simple site name rather than a long string of numbers.
Cybercriminals can monitor DNS requests to track your movements online, but a VPN’s DNS resolution system is designed to thwart them with further encryption. Avast protects IPv4 traffic behind a firewall and also disables IPv6 requests.
Is a VPN worth it?
It’s always worth using a VPN to enhance online privacy, protect sensitive data, and help access the content you love. While potential drawbacks include slightly lower download speeds and increased data usage, the overwhelming benefits provided by robust data encryption and content access make VPNs invaluable digital safety tools.
Benefits of using a VPN
Our guide to the benefits of a VPN will give you a detailed explanation, but here’s a quick rundown of the pros of VPN usage:
-
Stream from anywhere: By altering your virtual location, you may be able to access your favorite streaming content on the go.
-
Access blocked websites: The encrypted connection provided by your VPN will tunnel right through certain restrictions and help you bypass content blocks.
-
Avoid censorship: Help sidestep certain government restrictions by hiding your real location and encrypting your traffic.
-
Beat price discrimination: By masking your location, a VPN can allow you to access region-specific pricing and avoid inflated costs based on your real location.
-
Avoid tracking: Help prevent some tracking by hackers, cybercriminals, corporations, the government, and even your own ISP.
-
Network privacy: Keep your online activity hidden from other people connected to your local network.
-
Prevent bandwidth throttling: Encrypting your internet traffic helps prevent your ISP from detecting specific activities like streaming or gaming and deliberately slowing them down.
Avast SecureLine VPN will secure your connection, no matter if you’re at home or on public Wi-Fi. Use our VPN on all your devices to get real digital privacy. Access your favorite content, avoid price discrimination, and keep your private matters private.
Negatives of using a VPN
As with any type of technology, there are also some disadvantages and limitations to using a VPN:
-
Potentially slower speeds: Your web traffic goes through more steps than usual when connected via VPN, so your ping will increase. But you can always take steps to speed up your VPN connection.
-
QoS challenges: QoS (quality of service) describes the performance of a service or network. But VPNs have no standard metrics, so you need to rely on professional reviews and word-of-mouth to learn what’s most reliable.
-
VPN blocks: Some companies attempt to block access from known VPN IP addresses, but VPNs can often get around this by creating new virtual IP addresses.
-
No cookie protection: A VPN can’t block cookies — that’s why you should also use a private browser, like Avast Secure Browser, to help prevent web tracking.
-
Not total privacy: The VPN provider itself can see your internet activity if they want. That’s why it’s so important to choose a trustworthy provider that doesn’t keep logs of your internet habits.
And remember, while VPNs do help protect against identity theft by keeping your sensitive information private, they can’t stop data breaches from occurring. If you suspect you’ve fallen victim, it’s crucial that you report identity theft quickly to help mitigate damages, then take steps to remove your personal information online and help prevent identity theft from happening again.
So are VPNs worth it? Absolutely. No tool is perfect, but the powerful and wide-ranging benefits VPNs provide should form a vital component of your online privacy and security arsenal.
Different types of VPN
VPNs come in various types, each tailored to different needs and use cases. From remote access VPNs designed for individual users to site-to-site VPNs for organizations, understanding the distinctions helps you choose the right solution.
Here’s a closer look at the different types of VPNs you’re likely to encounter:
Remote-access VPNs allow users to connect to another network through a private encryption tunnel.
 A remote-access VPN lets you connect to a company’s internal server or the public internet.
A remote-access VPN lets you connect to a company’s internal server or the public internet.
Site-to-site VPNs, also called router-to-router VPNs, are mostly used within corporate environments, specifically when an enterprise has headquarters in several different locations.
 A site-to-site VPN is used to create an intranet.
A site-to-site VPN is used to create an intranet.
Double VPNs use VPN server chaining to route internet traffic through two separate VPN networks. They encrypt network data twice, offering an even more private and secure VPN connection.
There are also specialty VPNs designed for specific tasks — like a P2P VPN server for file sharing and downloading.
VPNs also vary according to the VPN protocols they use to secure your internet data. The most common protocols include:
-
PPTP
-
IKEv
-
L2TP/IPSec
-
SSL
-
TLS
-
SSH
-
WireGuard
-
OpenVPN
Each protocol has advantages, disadvantages, and specific use cases. Whereas PPTP is now largely considered obsolete, OpenVPN is among the most secure because it’s open-source, which helps in the discovery and patching of vulnerabilities. But if you’re willing to sacrifice a little security for speed, WireGuard is the top performer.
No matter which type of VPN you opt for, choose one like Avast SecureLine VPN, which has a strict VPN policy, meaning we don’t keep or share logs or other records of users’ browsing history, downloaded files, or other online activity.
Do I need a VPN?
A VPN is an essential tool for staying secure online. Routinely using a VPN to connect to the internet encrypts your data, protects your privacy, and shields you from a variety of cyber threats. Whether avoiding tracking, bypassing geo-restrictions, or ensuring secure communication, a VPN safeguards your online activities and allows you to surf more freely.
But there are times when securing your internet connection is even more important than usual. Here are the situations where you should always make sure you have your VPN enabled:
-
Using public Wi-Fi: Insulate yourself against sniffing or evil twin attacks by hackers lurking on public networks.
-
Online shopping: A VPN secures your payment details and personal data, protecting you from hackers and fraudulent sites.
-
Gaming: By reducing the risk of Distributed Denial of Service (DDoS) attacks and bypassing regional restrictions, VPNs ensure a smoother, safer gaming experience.
-
Using streaming services: Access to geo-restricted content becomes possible, allowing you to enjoy shows and movies from different regions.
-
Traveling: Your data stays protected on public Wi-Fi, and VPNs help you access your favorite content on the go.
Are VPNs better than Tor?
VPN protection is the closest you can get to true anonymity online without using the Tor network, which bounces your connection around a widely distributed network of volunteer relays. VPNs do not use this (very slow) protocol, instead offering a balanced combination of powerful encryption with high performance and flexibility.
Can I use a VPN on any device?
Any device that connects to the internet will benefit from the privacy VPNs provide. Most VPN providers offer their services on multiple platforms. Avast SecureLine VPN will cover up to ten devices — PC, Mac, Android, and iOS — with one account.
 VPNs work on PCs, tablets, and mobile phones.
VPNs work on PCs, tablets, and mobile phones.
Desktops, laptops, tablets, and phones can all connect individually to a VPN. For IoT devices, the best option is to set up your router with VPN protection.
 Use a VPN on your router to protect your privacy on all your connected devices.
Use a VPN on your router to protect your privacy on all your connected devices.
What to look for when choosing a VPN
Choosing the right VPN involves considering several important factors to ensure your privacy, security, and online experience are optimized. From speed and encryption standards to customer support and features, evaluating these aspects will help you select a VPN that best suits your needs for browsing, streaming, and online protection.
-
Speed: Ensure the VPN is fast enough for streaming or downloading without interruptions.
-
Reputation: Read consumer and expert reviews to verify the VPN's performance and legitimacy.
-
Shared IP addresses: Using shared IPs enhances privacy by mixing your activity with other users.
-
Servers: More servers mean less crowding, and geo-optimized servers provide faster, more reliable connections.
-
Encryption: Choose AES-256 encryption for top-tier security and virtually unbreakable protection.
-
Protocol: Opt for reliable protocols like OpenVPN and avoid weaker ones like PPTP.
-
Policy: Verify the VPN has a strict no-logs policy to protect your private data.
-
Customer support: Ensure 24/7 customer support is available for troubleshooting.
-
Features: Look for features like BitTorrent compatibility, ad-blocking, firewalls, kill switches, simultaneous VPN connections, or the ability to change your IP address and server location at will.
Should I get a free VPN?
You should avoid free VPNs as they often have weak security protocols like PPTP instead of WireGuard or OpenVPN, limited servers that result in slow speeds, intrusive ads, and strict download limits. You’re better off opting for a reliable, paid VPN for better performance and protection. Avast SecureLine VPN even comes with the option of a free trial.
History of VPNs — when was the VPN invented?
VPNs were invented by Microsoft in 1996 as a way for remote employees to securely access the company’s internal network. Then, in 2005, consumer-level VPNs were introduced to grant individuals all the benefits of online privacy that they entail. VPNs continue to be used for this purpose all around the world, albeit with increasingly enhanced and expanded feature sets and levels of sophistication.
How do I set up a VPN?
It’s usually super easy to set up a VPN — just go to your chosen service’s download page. Once you download Avast SecureLine VPN and launch the app, it will start working with the touch of a button. The same is true no matter which device you use it on.
Should I leave my VPN on all the time?
It’s generally a good idea to leave your VPN enabled so that you’ll always reap the security and privacy benefits. However, a VPN requires additional bandwidth and increases latency, so turning it off may help to fix slow internet speeds. Plus, services and websites with specific regional restrictions or access limitations may have limited functionality if you’re connected to a VPN server that’s overseas.
Is my VPN working?
To find out if your VPN is working, go to whatismyipaddress.com and see if the location matches the location shown by your VPN.
Use a secure VPN connection you can trust
Wondering how to download a VPN? We can help with that — click the button below and we’ll guide you through the easy setup process. Avast SecureLine VPN offers breakneck speeds and top-of-the-line features. Plus, it gives you ironclad security with AES-256 bank-grade encryption and the OpenVPN protocol. Give it a spin now with our free trial.