What is private browsing mode?
Private browsing mode is a feature that hides your internet activity from anyone who uses your device. When you use your browser’s private mode, your search history, passwords, and other browsing data aren’t saved on your device. That means when other people use your device, they won’t see what you did during your private browsing session.
Incognito mode is the same as private browsing — Incognito mode is simply what Chrome calls private browsing.
After browsing in private mode, your search history and cookies are wiped clean, so if anyone borrows your device they won’t know which websites you visited or what you entered into search engines. If you search for presents while browsing in private mode, no one in your family will see what you searched for if they use your device later.
While private browsing, or going incognito, removes most traces of your browsing activity from your computer or phone, it does not mean you stay anonymous online — and it does not protect you from web tracking.
What’s the difference between private browsing and anonymous browsing?
Private browsing mode clears your cookies and other browsing data only on your device. What you do online — visiting websites, searching for gifts, clicking links, planning trips — can still be tracked by advertisers, your internet service provider (ISP), the government (if they’re looking), and potentially hackers.
Private browsing mode also won’t protect you from phishing scams or other online threats, so always check the safety of the websites you visit. But private browsing is a good first step, and incognito mode is safe and easy to use.
Unlike private browsing mode, anonymous browsing hides your IP address and other online identifying information so that your internet activity can’t be traced back to you at all. So if you want true anonymity while browsing, you need to use additional tools like a VPN.
How to turn private browsing mode on and off
No matter which web browser you use, it’s easy to turn private browsing mode on and off. In most browsers — like Chrome, Firefox, and Edge — all windows and tabs are part of the same private browsing session, meaning they share browsing data among them. On Mac and iPhone, Safari treats each private tab and window as an entirely separate session.
Read on for instructions on how to start using private browsing mode and how to turn off incognito mode in Chrome, Firefox, Safari, Microsoft Edge, and Avast Secure Browser.
And be sure to check out our guide to the best browsers for privacy and our review of the fastest web browsers.
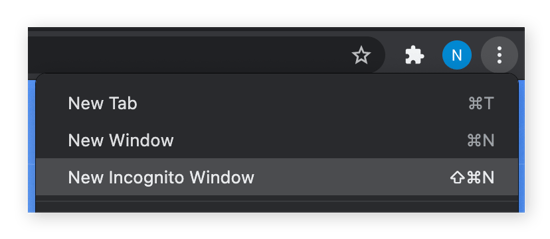
Private browsing in Google Chrome
Here’s how to turn on private browsing on Google Chrome:
-
Open Chrome browser.
-
Click the three dots in the top-right corner and select New Incognito Window.
-
Or, you can use a keyboard shortcut to enter private mode. On Windows, hit CTRL + Shift + N to open a new incognito window. On a Mac, use Command + Shift + N.
And that’s it. You’re now browsing privately in an incognito window, meaning the cookies and internet search history from your session won’t be saved after you close private mode. But remember that Google can still track and use your data while you’re in private mode.
If you’ve been browsing normally without incognito mode, check out our guides to deleting your cookies and clearing your search history.
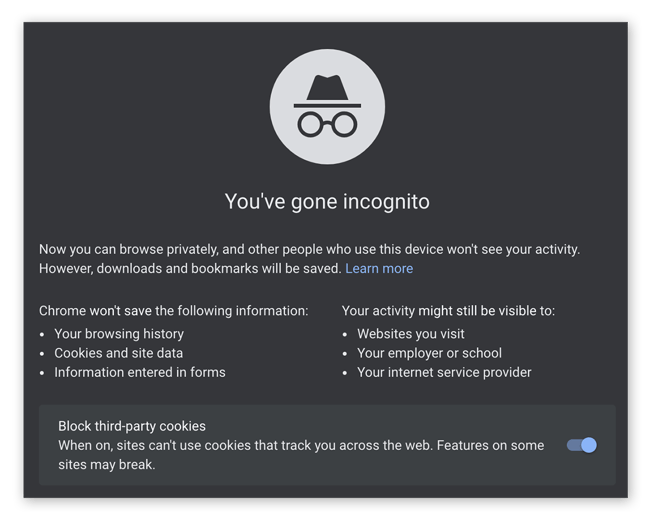
If you want to know how to turn off incognito mode on Chrome, simply close all of your incognito windows and you’ll be right back to normal browsing.
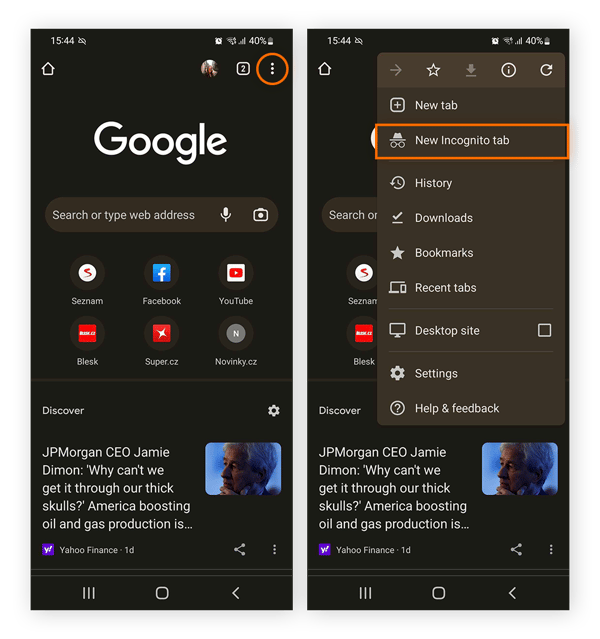
Private browsing in Google Chrome Mobile
Want to use Incognito mode on Mobile? Here’s all you need to do:
-
Open Google Chrome on your mobile device.
-
Tap the three dots at the top on the screen and select New Incognito tab.
-
You’re now browsing privately, meaning your search history is disabled and browsing data will be deleted at the end of your session.
Private browsing in Safari (incognito)
It’s easy to begin a private browsing session in Safari. Here’s how:
-
Open Safari and click File on the top menu bar.
-
Select New Private Window.

-
You can also use the keyboard shortcut Command + Shift + N to start browsing privately on Safari in a snap.
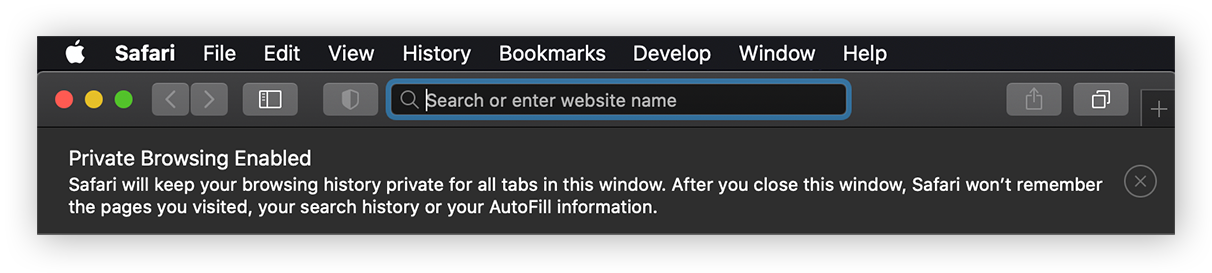
To turn off private browsing in Safari, just close all your private windows and you’ll be browsing normally again.
Private browsing on an iPhone and iPad in Safari
If you’re on an iPhone or an iPad, here’s how to turn on private browsing on Safari:
-
Open Safari on your iPhone or iPad.
-
Tap the Tabs icon in the bottom-right corner of the screen, and then tap “(number) Tabs” at the bottom of the screen.
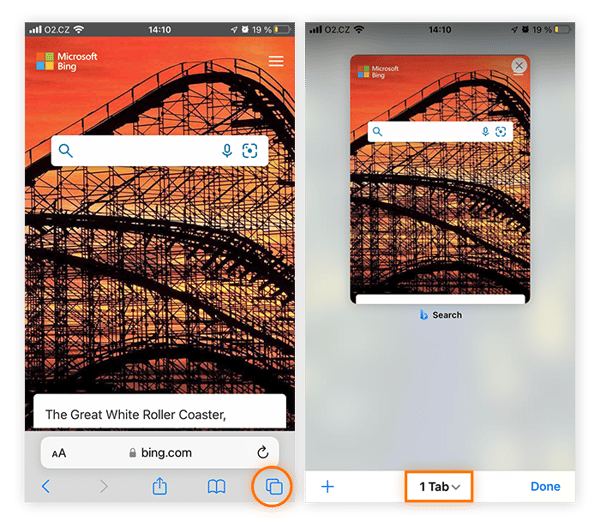
-
Tap Private when the Tab Groups list displays, and then tap Done to start browsing incognito on Safari on your iPhone or iPad.

Private browsing in Firefox
It’s just as easy to go incognito in Firefox. Here’s how:
-
Open Firefox.
-
Click the three lines (the hamburger menu) in the upper-right corner.
-
Select New Private Window.
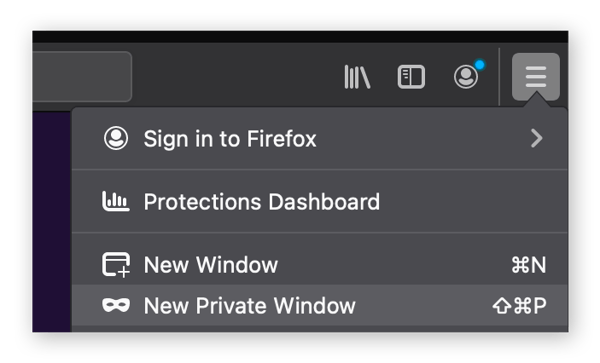
-
You can also use a keyboard shortcut to browse privately in firefox: use CTRL + Shift + P on Windows or Command + Shift + P on Mac.
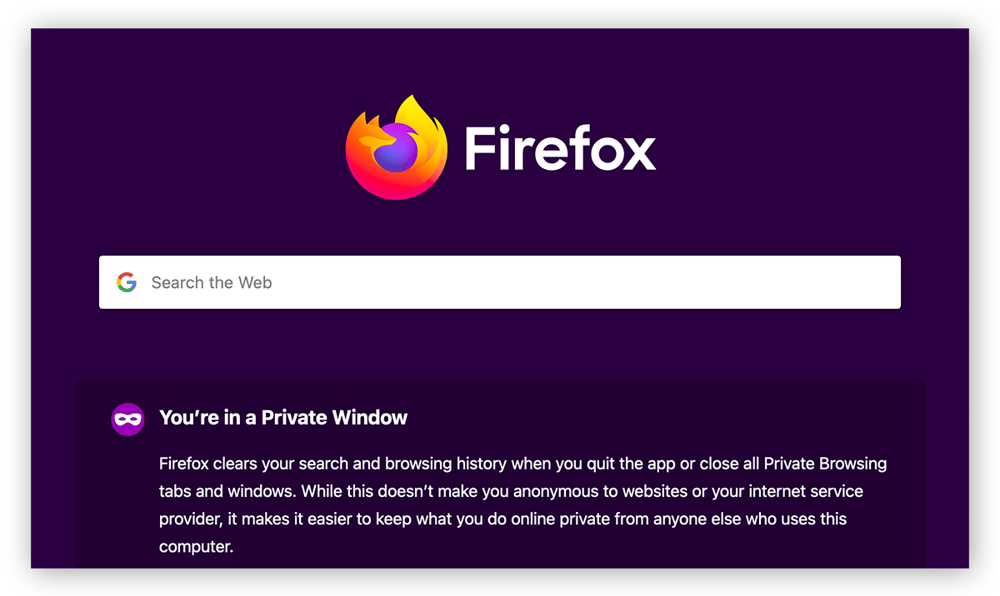
If you’re wondering how to turn off private browsing in Firefox, simply close all your private windows, and you’ll automatically start browsing normally again.
Private browsing in Firefox on Android
Here’s how to enable private search and browsing in Firefox on Android:
-
Open Firefox on your Android device.
-
Tap the eye-mask private browsing icon in the top-right.
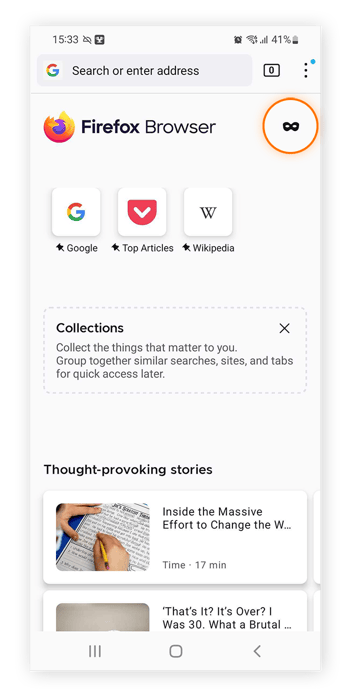
And that’s it — you’re now browsing incognito using Private Firefox mode.
Private browsing in Internet Explorer and Edge (InPrivate browsing mode)
Just as Internet Explorer’s private browsing feature was called InPrivate browsing, Microsoft Edge also supports a private browsing feature called InPrivate browsing. Here’s how to use it:
-
Open Microsoft Edge and click the three dots in the upper-right corner.
-
Select New InPrivate window.
-
Alternatively, use the keyboard shortcut CTRL + Shift + P to open an InPrivate window in Edge.
After you open a private window and go incognito in Edge, you’ll see “InPrivate” in a blue band around your avatar in the upper-right corner of your browser window.

Note: Internet Explorer has now been retired by Microsoft and is no longer updated with security fixes. That means IE may contain software vulnerabilities that hackers can exploit. Stay protected by updating to Edge or changing your default Windows browser.
Private browsing in Microsoft Edge on mobile
Follow these steps for private browsing on mobile in Microsoft Edge’s InPrivate browsing mode:
-
Open the Microsoft Edge browser on your phone.
-
Tap the Tabs button on the lower-right of the screen and select InPrivate in the top-left corner.
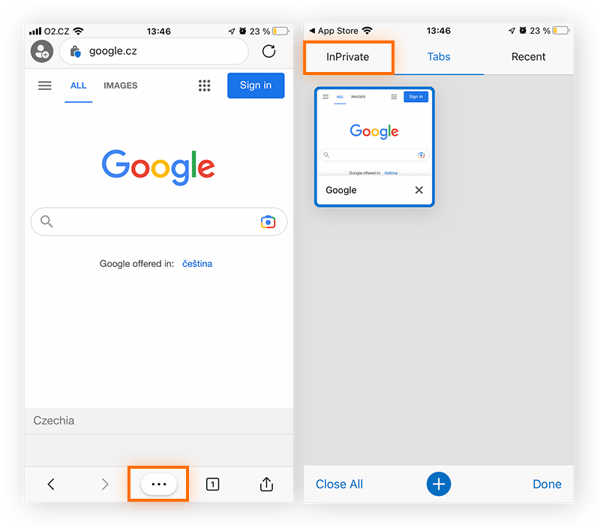
-
Then, either tap on an existing InPrivate tab to continue a session or tap the + button at the bottom to open a new private mode tab.
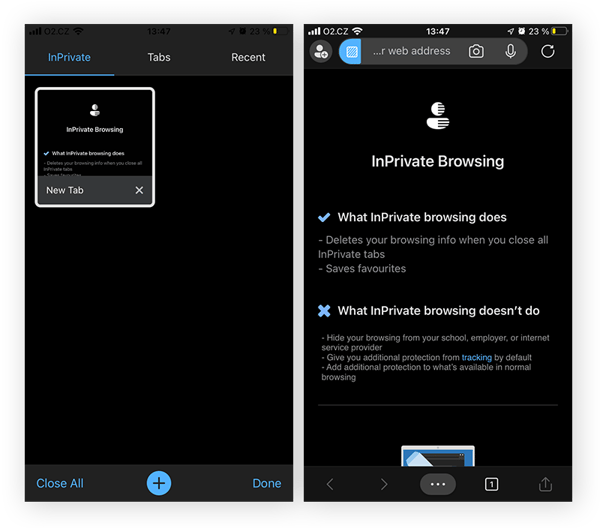
Private Browsing in Avast Secure Browser
For more security and privacy than just using incognito mode, use a top-rated privacy-focused browser, like Avast Secure Browser. In addition to ad blocking, anti-tracking, and an array of other privacy protections, Avast Secure Browser has a private mode, too. Here’s how to use it:
-
Download and install Avast Secure Browser.
-
Click the three dots in the upper-right corner and select New Private Mode Window.
-
Or, use a keyboard shortcut. For Windows: CTRL + Shift + N. For Mac: Command + Shift + N.
-
Now you’re in Private Mode!
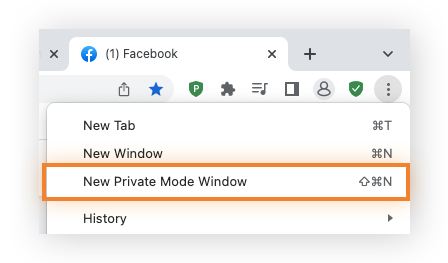
Private browsing in Avast Secure Browser on mobile
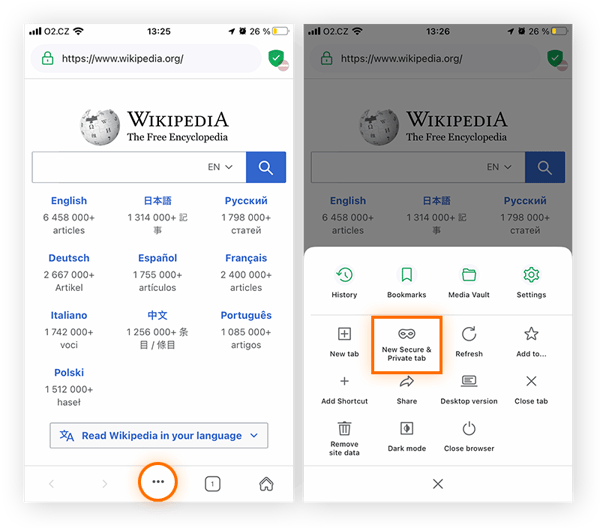
You can use Avast Secure Browser’s Private Mode on mobile, too. Here’s how to enable Private Mode on the mobile browser app:
-
Open Avast Secure Browser on your mobile device.
-
Tap the three dots at the bottom on the screen and select New Secure & Private Tab from the menu.
-
And that’s it — you’re now browsing in Private Mode on one of the best secure and private browsers available.
Is private browsing really private?
Private browsing hides your searches and browsing activity from other people who use your computer, but it doesn’t mean your activity can’t be tracked. Private browsing does not hide your internet activity from third-parties like the websites you visit, advertisers, ISPs, the government, or hackers. And browsing in private mode does not prevent web tracking.
Some browsers can block tracking cookies while in incognito mode, but they can’t block more advanced tracking techniques like browser fingerprinting, which can identify you online with remarkable accuracy. Private browsing also does not hide your IP address, which is another way you can be identified online.
How can I see what has been viewed in private browsing mode?
If you’re wondering how to see what someone else has done during their private browsing session, the answer is simple — you can’t. That’s what private browsing is for. If you’re that curious to know what your partner got you for the holidays, you’ll just have to wait.
But even though browsing history isn’t stored on your device, private browsing doesn't completely obscure evidence of your online activity. So if you’re looking to retrace your steps or cover your tracks completely, here’s how to view and delete incognito history.
If you’re a parent trying to see if your child has been looking at inappropriate content online, you do have some options. You won’t be able to unearth their past private browsing sessions, but you can introduce content filters. A parental control app can help you block explicit content, set screen time limits, and even pause internet access with the tap of a button.
Get more privacy than private browsing mode or incognito
Private browsing may not offer true online privacy, but there are options to protect your personal information and stay anonymous online.
One of the easiest ways is to use a browser built specifically for privacy and security. Avast Secure Browser offers advanced anti-tracking protection, anti-fingerprinting technology, and a suite of additional privacy and security features.

Block ads and web trackers, keep your most sensitive information secure with Bank Mode, and enjoy smoother, faster browsing with Avast Secure Browser. Install it today and level up your online privacy.